
The Lazarus group leveraged a supply chain attack to target users located in South Korea with custom malware.
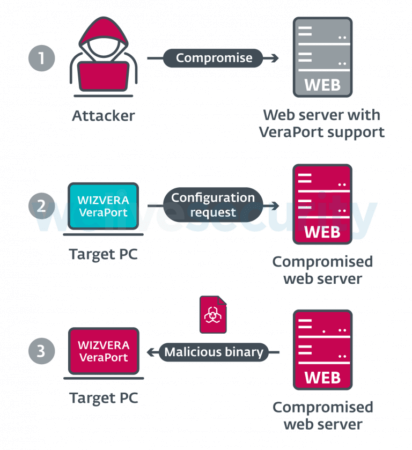
On November 16, ESET disclosed that the Lazarus group conducted its supply chain attack by abusing WIZVERA VeraPort. This application helps users in South Korea manage the installation of additional computer security software when they visit a government portal or banking website that requires it.
Users sometimes can't access a site's resources unless they have WIZVERA VeraPort installed on their devices.
Acknowledging that reality, the Lazarus group crafted its attack to prey upon machines that had WIZVERA VeraPort installed.
They specifically used stolen code-signing certificates, including one lifted from a U.S. branch of a South Korean security company, to push out malware in the VeraPort software bundle served by a legitimate but compromised website.
The attackers wasted no effort in making their malware payloads appear legitimate. As quoted by ESET in its research:
The attackers camouflaged the Lazarus malware samples as legitimate software. These samples have similar filenames, icons and VERSIONINFO resources as legitimate South Korean software often delivered via WIZVERA VeraPort. Binaries that are downloaded and executed via the WIZVERA VeraPort mechanism are stored in %Temp%\[12_RANDOM_DIGITS]\.
The final malware payload arrived with functionality typical of a Remote Access Trojan (RAT). The threat used those capabilities to target a victim's filesystem as well as to download and install additional tools used by the malicious actors.
ESET ultimately attributed the supply chain attack to the Lazarus group based upon the network infrastructure and toolset that factored in the campaign, the selection of South Korean targets as victims and other indicators.
News of this attack arrived several months after security researchers discovered a multi-platform malware framework called “MATA” that the Lazarus group had used to target victims worldwide.
Zero Trust and the Seven Tenets
Understand the principles of Zero Trust in cybersecurity with Tripwire's detailed guide. Ideal for both newcomers and seasoned professionals, this resource provides a practical pathway to implementing Zero Trust, enhancing your organization's security posture in the ever-evolving digital landscape.

