
Magecart threat actors used the same skimmer against two web-based suppliers to try to steal users' payment card information. As discovered by security researcher Willem de Groot, the first attack occurred at 15:56:42 GMT on 10 May when bad actors injected the skimmer into the bottom of a script used by enterprise content management system CloudCMS. https://twitter.com/gwillem/status/1127619061725241349 This malicious action targeted version 1.5.23 of the script, which limited the scope of this attack. According to RiskIQ, version 1.5.23 affects just 20 percent of sites using CloudCMS. Even then, RiskIQ observed that only a few hundred websites were using CloudCMS scripts at the time of detection. Those using the affected version of the script were less numerous still. The Magecart attackers also leveraged the script against analytics provider Picreel, observed de Groot. In that instance, they inserted the skimmer at the bottom of a script used by Picreel to track user behavior. But the attackers made a mistake in that they broke the file's JavaScript syntax, which caused the script to not execute in certain browsers. In contrast to the CloudCMS case, RiskIQ found that hundreds of sites were using the affected script. But the issue described above likely limited the number of times that the skimmer was able to execute in a user's browser.
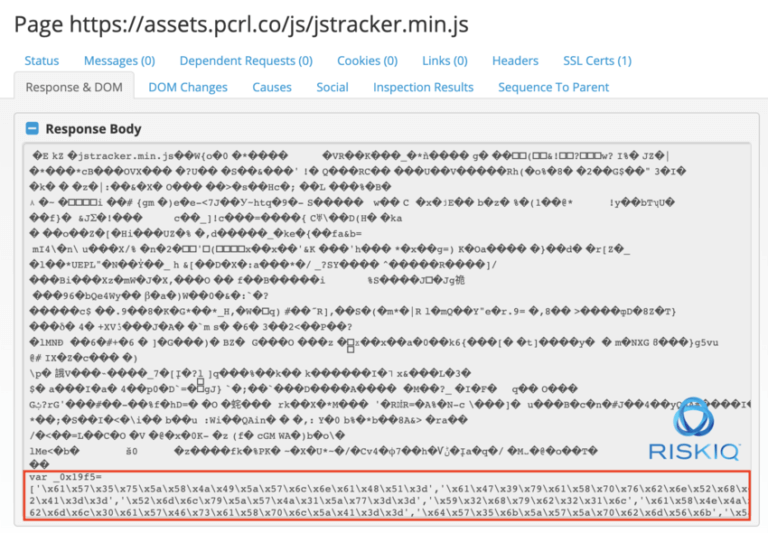
The Magecart skimmer affecting Picreel. (Source: RiskIQ) RiskIQ believes that these two instances highlight how bad actors are increasingly becoming more efficient in their ability to launch supply chain attacks. This is concerning given the limited visibility which many organizations possess over their web-facing attack surface. As the firm explains in a blog post:
... [I]t takes less time than ever for consumers to see their data stolen, seemingly out of nowhere. In the end, it doesn’t matter to consumers whether this happens as the result of a traditional breach or a web-based supply chain attack. The reputation of organizations that run payment forms online is at stake, as well as the overall confidence of online shoppers.
To help defend against attacks such as the ones described above, RiskIQ recommends that organizations improve their visibility and invest in monitoring their entire attack surface. News of these compromises follows just a few months after a criminal Magecart gang successfully compromised hundreds of e-commerce websites via a malicious script that silently harvested personal data and payment card information as customers bought goods and services online.

