
A malvertising campaign is redirecting users to the RIG exploit kit for the purpose of loading ERIS ransomware onto vulnerable machines. Over the 5-7 July weekend, security researcher nao_sec discovered a malvertising campaign that was abusing the popcash ad network to redirect users to a landing page for the RIG exploit kit. The researcher told Bleeping Computer that this threat scanned the user's computer for signs of a specific Shockwave (SWF) vulnerability. If that weakness was unpatched on the user's computer, the RIG exploit kit ran its exploit code in order to download ERIS. The ransomware sample analyzed by nao_sec appended the .ERIS extension to each file it encrypted. It also added the "_FLAG_ENCRYPTED_" file marker at the end of every file it affected. At that point, ERIS ransomware created a ransom note entitled "@ READ ME TO RECOVER FILES @.txt" that informed the victim to contact Limaooo@cock[dot]li for payment instructions. The note also came with an infection ID which the ransomware developers allegedly used to perform a test decryption of an affected file.
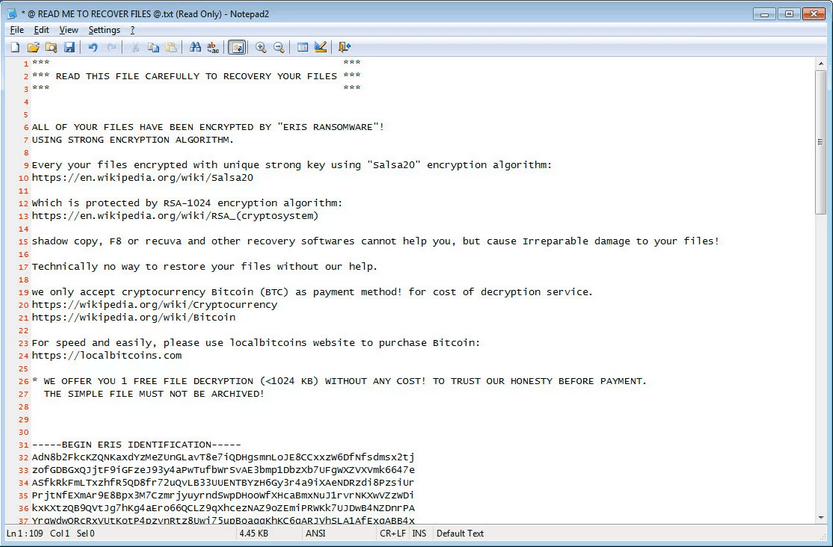
The ransom note for ERIS ransomware (Source: Bleeping Computer) This isn't the first time that nao_sec has discovered an attack campaign in which RIG exploit kit pushed some family of crypto-malware. As reported by Bleeping Computer, the security researcher spotted a malvertising campaign redirecting users to the exploit package in early-June 2019. The RIG exploit kit attempted to exploit vulnerabilities affecting Internet Explorer in order to drop Buran ransomware as its payload. As of this writing, victims of ERIS ransomware have no means of recovering their affected files for free. It's therefore up to organizations and users to protect themselves against an ERIS ransomware infection. They can start by following these tips designed to prevent a ransomware infection in the first place. Organizations might also want to take things a step further and strengthen their ability to defend against advanced malware. Learn how Tripwire's malware detection solution can help in that regard.

