
Security researchers attributed a spike in Snake ransomware activity to a new campaign that's targeted organizations worldwide. Snake ransomware first attracted the attention of malware analysts in January 2020 when they observed the crypto-malware family targeting entire corporate networks. Shortly after this discovery, the threat quieted down. It produced few new detected infections in the wild for the next few months. That was until May 4, when ID Ransomware registered a sudden spike in submissions for the ransomware.
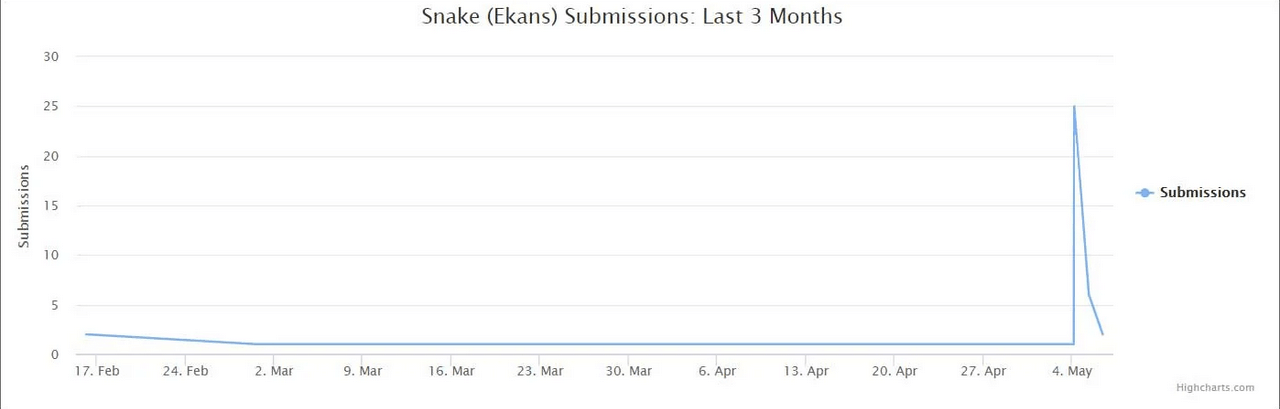
ID Ransomware's data for Snake (Source: Bleeping Computer) As reported by Bleeping Computer, these submissions were part of a large campaign that targeted organizations around the world. Among those hit by Snake ransomware in this campaign was Fresenius, Europe's largest private hospital operator. A spokesperson for Fresenius confirmed to KrebsonSecurity that the organization was grappling with an infection of malicious software:
I can confirm that Fresenius’ IT security detected a computer virus on company computers. As a precautionary measure in accordance with our security protocol drawn up for such cases, steps have been taken to prevent further spread. We have also informed the relevant investigating authorities and while some functions within the company are currently limited, patient care continues. Our IT experts are continuing to work on solving the problem as quickly as possible and ensuring that operations run as smoothly as possible.
A source told the computer self-help site that the ransomware had also claimed a French architectural firm and a prepaid debit card company as victims. Organizations should take this campaign seriously, especially after security researchers found that Snake had begun mimicking other families by threatening to publish the data of victims who refused to pay their ransoms. In response, organizations should consider taking steps to prevent a crypto-malware infection in the first place. They can use these steps to begin securing their assets against a ransomware attack.

