What's this Maze thing I keep hearing about?
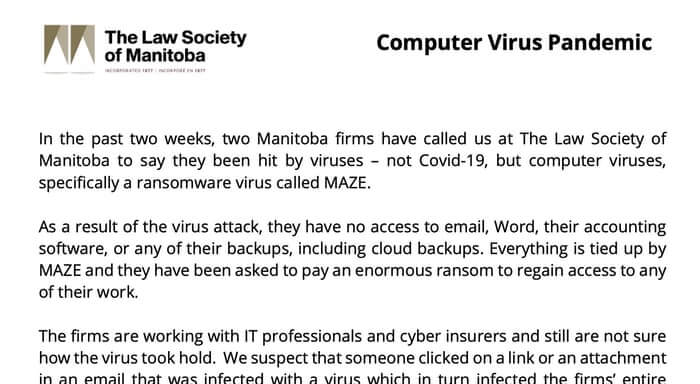
Maze is a particularly sophisticated strain of Windows ransomware that has hit companies and organizations around the world and demanded that a cryptocurrency payment be made in exchange for the safe recovery of encrypted data.
There's been plenty of ransomware before. What makes Maze so special?
Like other ransomware seen in the past, Maze can spread across a corporate network, infect computers it finds and encrypts data so it cannot be accessed. But what makes Maze more dangerous is that it also steals the data it finds and exfiltrates it to servers controlled by malicious hackers who then threaten to release it if a ransom is not paid. Increasingly, other ransomware (such as REvil, also known as Sodinokibi) have been observed using similar tactics.
So simply restoring from a backup..?
...isn't enough. Yes, restoring your data from a secure backup can get you back up and running again (if the backup hasn't itself been compromised, of course), but it doesn't undo the fact that criminals now have a copy of your company's data.
Nasty. So this is a combination of a ransomware attack and a data breach?
Yup. And as a website operated by the criminals behind the Maze attacks claims, if the ransom is not paid, they will:
- Release public details of your security breach and inform the media
- Sell stolen information with commercial value on the dark market
- Tell any stock exchanges on which your company might be listed about the hack and the loss of sensitive information
- Use stolen information to attack clients and partners as well as inform them that your company was hacked.
This is much worse than just being hit by ransomware
Yes, it is. It appears that Maze ransomware gang is not only capable of writing sophisticated malware. They have also found a very effective way of increasing the pressure on its corporate "clients" to pay up. One has to assume that the attackers saw that many organizations now have more rigorous backup regimes in place and realized that they needed to up the ante if they were to maximize their potential criminal earnings.
How much information does the Maze ransomware typically steal from a company?
It's hard to say, as only the companies concerned and the criminals themselves will know how much has been taken. However, the Maze website has this to say:
Usually we have over 100Gb of data from single client. Sometimes up to 10Tb of commercial and private information. We are looking for NDA marked information and everything that can be used as a base for the lawsuit agains our client.[sic]
Wait. You mentioned this before. The Maze guys have a website?
Yes, on their website they list their "new clients" (their term for recent corporate victims who have failed to pay up and who might be trying to keep news of their security breach out of the press.) The website includes details of when victims had their computer systems hit by the Maze ransomware as well as links to downloads of stolen data and documents as "proof." There are even convenient buttons on the website to share details of breaches via social media.
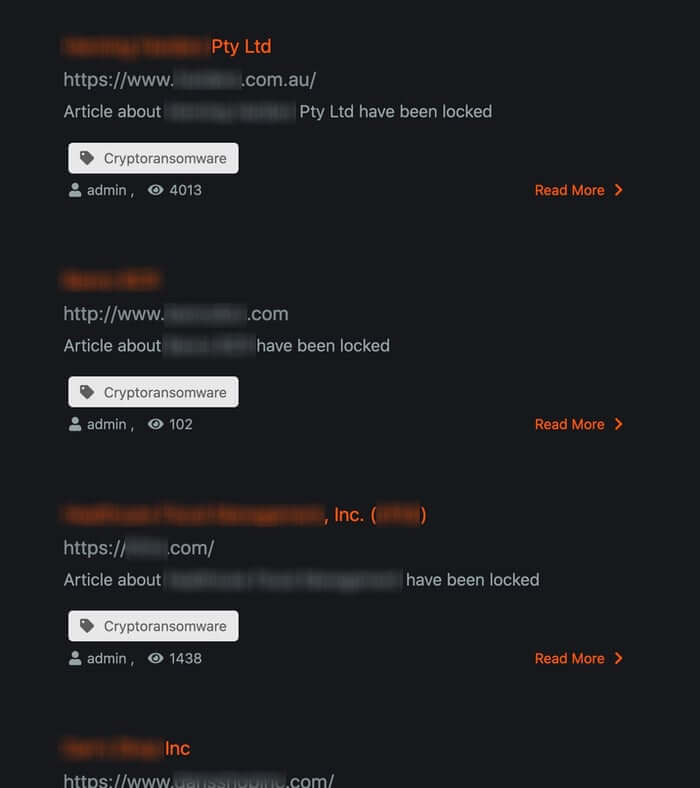
In the above image, I've blurred out the names of Maze victims exposed on the cybercriminals' website. Sadly, the hackers have no qualms about offering unredacted downloads of the data they have stolen.
This is terrifying. What types of organizations have been hit by Maze?
Cognizant, the multinational IT services giant, revealed last week that it had been hit by Maze. Other victims have included medical research organisations, professional security services and law firms.
How does the Maze ransomware infect an organization in the first place?
The attackers use a variety of different techniques to compromise your network. This can include exploitation of known vulnerabilities that have not been patched, remote desktop connections with weak passwords, malicious email attachments and/or links. In some cases, the attack may actually come from a client of yours or partner who has already fallen victim to the hackers.
So what should my company be doing to protect ourselves from the Maze ransomware?
You should still be making secure offsite backups. You should still be running up-to-date security solutions and ensuring that your computers are protected with the latest patches against newly-discovered vulnerabilities. You should still be using hard-to-crack, unique passwords to protect sensitive data and accounts as well as enabling multi-factor authentication. You should still be encrypting your sensitive data wherever possible. You should still be educating and informing staff about risks and the methods used by cybercriminals to electronically infiltrate organizations.
If my company has been unlucky enough to have been hit by the Maze ransomware, should we pay the ransom?
That ultimately is a decision that only you can make. Bear in mind that the more companies that pay a ransom, the more the criminals are likely to launch similar attacks in the future. At the same time, you may feel that your business needs to make the difficult but pragmatic decision to pay the criminals if you feel your company cannot survive any other way. Whatever your decision, we encourage you to inform law enforcement agencies of the incident and work with them to help them investigate who might be behind the attacks. And remember this: paying the ransom does not necessarily mean you have ridden yourself of the security problems that allowed you to be infected in the first place. If you don't find out what went wrong and why and fix it, then you could easily fall victim to further cybercrime attacks in the future. Check out this webinar to learn more about how leveraging basic security controls will help protect and detect ransomware attacks before significant damage is done: https://www.youtube.com/watch?v=udwr3V0ojIA&feature=emb_title
Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

