
It's one of Microsoft's best kept secrets. First released in 2009, the Enhanced Mitigation Experience Toolkit from Microsoft (EMET for short) has been helping companies reduce the risk of being exploited via unknown vulnerabilities in Windows and Windows applications. By detecting and preventing the buffer overflows and memory corruption vulnerabilities often exploited in zero-day attacks, the free EMET tool has often been recommended by Microsoft in security bulletins as a way of mitigating against exploits while they work on a proper patch. Through technologies such as Data Execution Prevention (DEP), Address Space Layout Randomization (ASLR) and pinning rules to validate digitally signed certificates while browsing, EMET can act as part of your layered defence. In short, you don't get rid of other technologies such as anti-virus software, but EMET helps sandbox Windows and Windows apps to make them harder to exploit, and prevent unpatched vulnerabilities from being successfully weaponised. Although primarily targeted at system administrators responsible for securing Windows PCs on larger networks because of the ability to manage and apply group policies, there's actually nothing to prevent you from also running EMET on your home computer if you wish to block common memory exploitation techniques and lock down applications. And this last week Microsoft has released the latest edition of EMET, version 5.5.
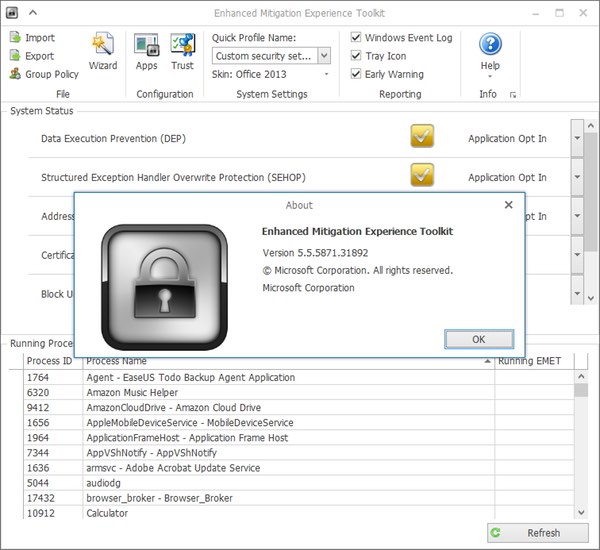
New features incorporated into EMET 5.5 include:
- Windows 10 compatibility
- Improved configuration of various mitigations via GPO
- Improved writing of the mitigations to the registry, making it easier to leverage existing tools to manage EMET mitigations via GPO
- EAF/EAF+ performance improvements
- Untrusted font mitigation for Windows 10
However, although EMET 5.5 is now officially compatible with Windows 10, Microsoft explains that users of the latest version of their operating system may not actually need it:
"EMET was released in 2009 as a standalone tool to help enterprises better protect their Windows clients by providing an interface to manage built-in Windows security mitigations while also providing additional features meant to disrupt known attack vectors used by prevalent malware. Since that time, we have made substantial improvements to the security of the browser and the core OS. With Windows 10 we have implemented many features and mitigations that can make EMET unnecessary on devices running Windows 10. EMET is most useful to help protect down-level systems, legacy applications, and to provide Control Flow Guard (CFG) protection for 3rd party software that may not yet be recompiled using CFG."
Microsoft points out that Windows 10 features such as Device Guard (which can lock a device down so only trusted applications can run), Control Flow Guard and AppLocker actually provide equivalent of better mitigations than EMET. And, of course, Windows 10's Edge browser is considered to be significantly more secure than the often beleaguered Internet Explorer. because every single web page you visit opens in its own "app container", effectively sandboxing threats. Do you use Microsoft EMET in your organisation? Have you found it an effective way to better protect your company, or did you find it caused additional problems? Leave a comment below with your experiences. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.

