
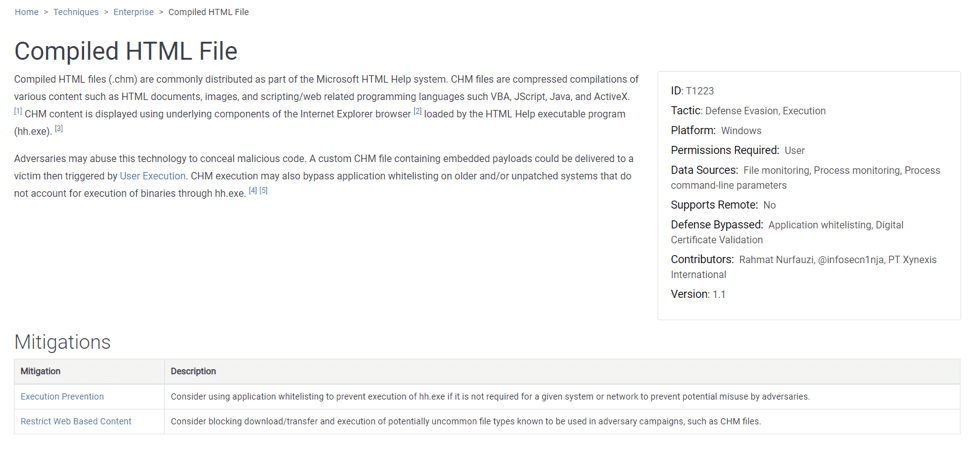
On the last day of July, MITRE released its most recent update to the ATT&CK framework. The ATT&CK framework is a curated knowledge base of tactics, techniques, software, that adversarial groups have leveraged when compromising enterprise systems. The July 2019 update is relatively minor compared to the April 2019 update, which saw a new tactic with 14 new Techniques. The current update centers around restructuring Mitigation content as well as new Groups and Software entries with no changes to Tactics or Techniques. Mitigations are now their own independent category instead of being annotations on individual Techniques. The consolidated 40 Enterprise Mitigations are represented, like Groups and Software, as objects and can be related to Techniques along with an annotation. For example, Compiled HTML File has two related Mitigations, Execution Prevention and Restrict Web Based Content, and Mitigations have their own field on Technique pages:
Mitigations have the same ID scheme as Mobile Mitigations (M####). As before, different Techniques can reference the same type of Mitigation with individualized annotations, but now each Mitigation has an entry that relates back to every associated Technique. Here’s Execution Prevention as an example:
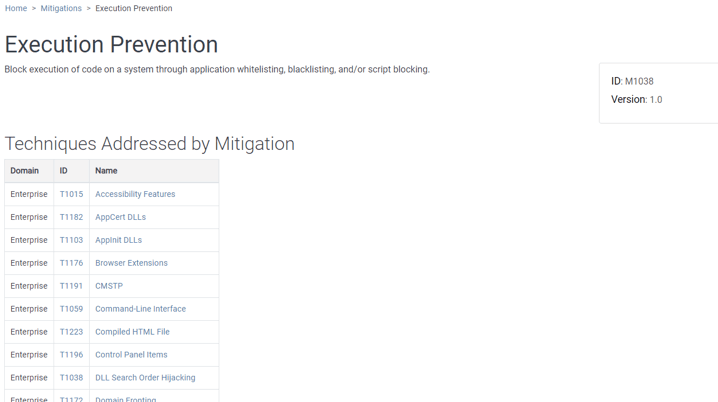
This is particularly useful to see which Techniques are addressed by a Mitigation. This allows security professionals to understand coverage in terms of Mitigations without searching through Techniques individually. The ATT&CK team has also done some house cleaning of Mitigations and some, like application whitelisting, which was pervasive across almost all techniques, were removed unless they applied directly to the technique. The old mitigation text is still available as STIX objects in the repository but does not show up on the website. We look forward to ATT&CK continually maturing. A complete list of changes for the July 2019 update can be found at https://attack.mitre.org/resources/updates/. You can learn more about the details of the ATT&CK framework through Travis Smith’s blog series, which breaks down the framework tactic by tactic.
Tripwire Enterprise: Security Configuration Management (SCM) Software
Enhance your organization's cybersecurity with Tripwire Enterprise! Explore our advanced security and compliance management solution now to protect your valuable assets and data.

