
A new modular backdoor detected as "Plurox" comes with multiple plugins that expand its capabilities to include cryptomining and worm-like behavior. In February 2019, Kaspersky Lab's researchers first detected the backdoor. Their analysis revealed that the backdoor, written in C, arrived with debug lines. This suggests that the malware was still in testing at the time of discovery. Additionally, the threat analysts observed that the malware used the TCP protocol to communicate with its command-and-control (C&C) server. This server, in turn, responded with one of several plugins. In one instance, Plurox used a plugin to install one of eight possible cryptominers depending on the infected system's configuration. In another example, the backdoor uses a UPnP plugin that enabled it to attack and gain a foothold on the local network. There's also an SMB plugin through which the malware was capable of exploiting EternalBlue to spread malware over the network. This plugin was identical to the wormDll32 module from Trojan.Win32.Trickster with some small differences. Kaspersky Lab clarified these similarities in its research:
As can be seen in these samples, not only is the injected code similar, but also the code for standard procedures. Based on this, we can assume that the analyzed samples were taken from the same source code (commented lines in the Trickster plugin are missing in the Plurox plugin), which means the respective creators of Plurox and Trickster may be linked.
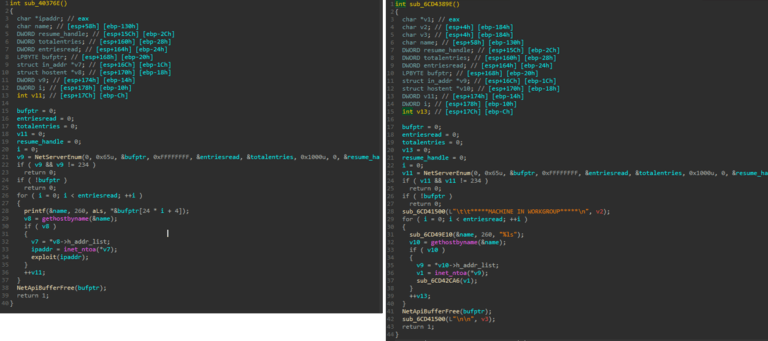
Left: Plurox SMB plugin NetServerEnum. Right: Trickster WormDll NetServerEnum. (Source: Kaspersky Lab) Plurox highlights the growing presence of modular malware in digital attackers' arsenals. Organizations should respond to this trend by protecting their critical assets against known malware threats as well as zero-day attacks. This tool should be capable of continuously monitoring the network for suspicious activity, examining suspicious files in a sandbox environment, delivering contextual reports for system changes and deploying quickly. Click here to learn how Tripwire Malware Detection can keep your organization safe against modular backdoors such as Plurox.

