
Research into recent ransomware submissions revealed that more than a tenth of crypto-malware infections now involve some element of data theft. In the second quarter of 2020, ID Ransomware received 100,001 submissions of crypto-malware pertaining to attacks that had targeted organizations and government entities. Of those attacks, 11,642 involved the theft of victim data by their perpetrators. That's over 11% of the attacks for that six-month period. These attacks involved numerous ransomware gangs. In March 2020, for instance, the Nefilim crypto-malware strain began telling its victims that it would publish their stolen data within a week unless they paid their ransom. That was about a month before the security firm learned of Ragnar Locker's demand of 1580 bitcoin (approximately $11 million) as ransom from Energias de Portuga (EDP), a Portuguese electric utilities company from which the attackers claimed to have stolen 10TB of data. Approximately a month after that, DoppelPaymer published a new entry on its data leaks site for the City of Torrance, CA.
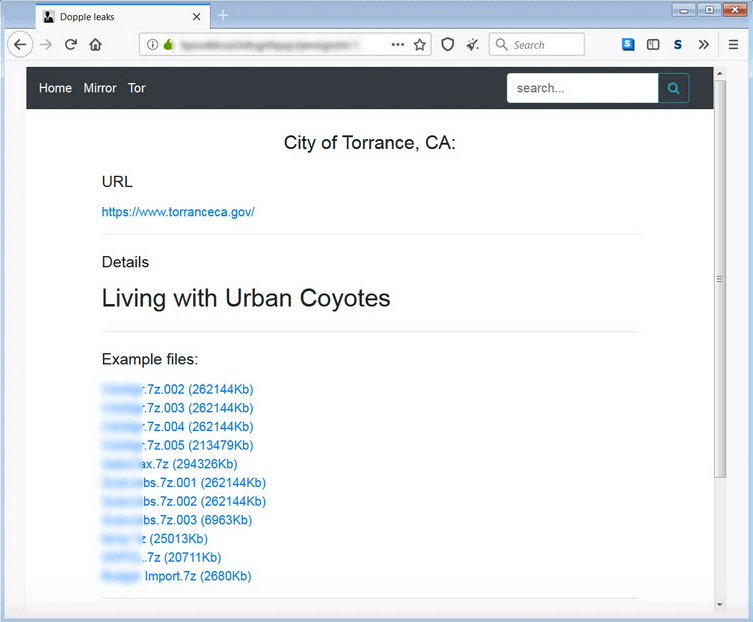
The “City of Torrance, CA” post published on DopplelPaymer's data leaks site. (Source: Bleeping Computer) Anti-malware and anti-virus software provider Emsisoft explained that ransomware attacks involving data theft could cause long-term damages to victims in the form of reputational harm, legal fines from lawsuits and regulatory penalties. The security firm noted that this type of attack could also open the door to additional digital threats. As quoted in its research:
... [E]xfiltration+encryption incidents create a path for future attacks and other criminal activity. The stolen information can be used to spear phish victim organizations’ clients and business partners or be used to commit other forms of fraud, such as business email compromise (BEC). In other words, one crime can lead to many.
Acknowledging those risks, it's imperative that organizations work to prevent a ransomware infection in the first place using these tips. They should also consider investing in a solution like Tripwire File Analyzer for the purpose of observing suspicious files' behavior in a quarantined environment.

