
A new ransomware strain called "Mount Locker" is demanding that victims pay multi-million dollar ransom payments to recover their data. According to Bleeping Computer, the ransomware first began making the rounds in July 2020. The malicious actors responsible for this threat took a cue from other crypto-malware gangs by stealing victims' unencrypted data and threatening to publish the data unless they received payment. In the case of Mount Locker, ransom demands sometimes climbed into the millions of dollars.
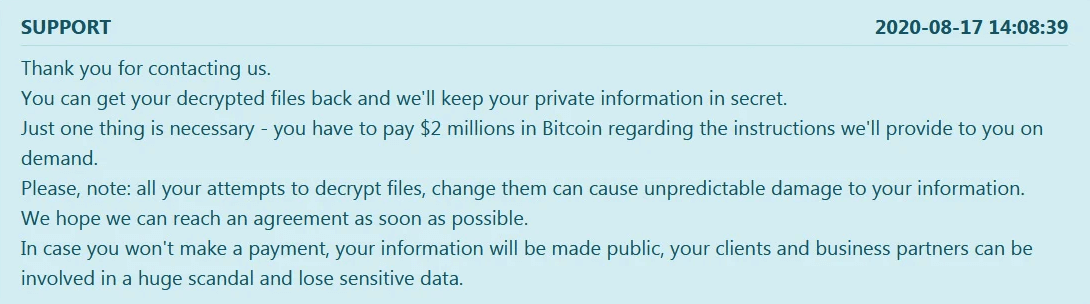
$2 million ransom demand from Mount Locker. (Source: Bleeping Computer) Mount Locker's handlers followed through on this threat after claiming to have stolen 400 GB from a victim. When the victim didn't pay, the attackers published their information on their data leak site. That site indicated that Mount Locker had affected four victims at the time of Bleeping Computer's writing. Of those, the data of just one victim was available for viewing on the site. An analysis of one sample by security researcher Michael Gillespie provided some insight into the ransomware's encryption routine. As explained by Bleeping Computer:
Mount Locker uses ChaCha20 to encrypt the files and an embedded RSA-2048 public key to encrypt the encryption key. From our analysis, when encrypting files, the ransomware will add an extension in the format .ReadManual.ID. For example, 1.doc would be encrypted and renamed to 1.doc.ReadManual.C77BFF8C, as shown in the encrypted folder below.
After completing its encryption routine, the ransomware registered its extension in the Registry so that its ransom note would load whenever the victim attempted to open one of their encrypted files. This message contained instructions on how the victim could go about to submit their ransom payment using Tor.
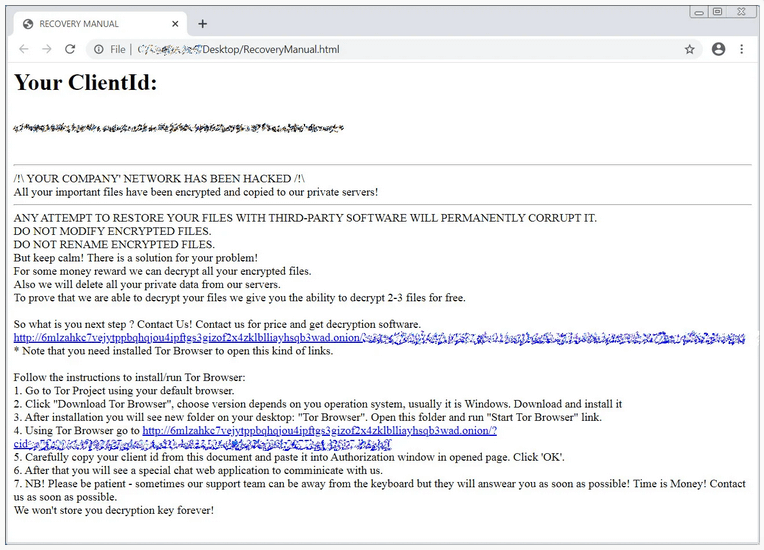
Mount Locker's ransom note. (Source: Bleeping Computer) Mount Locker suffered from no discernible weaknesses that made it possible for researchers to craft a free decryption utility at the time of analysis. It's therefore up to users and organizations alike to prevent a ransomware infection from occurring in the first place.

