
In my last post, I briefly summarized the evolution of network security. I will now discuss how network security strategies are no longer meeting the needs of organizations' increasingly complex IT environments.
A Different Strategy
Technological innovation has changed the nature of the network itself. No longer are employees limited to their workstation or possibly a laptop for connecting to the corporate network and doing their work. The use of tablets, mobile devices, and laptops are becoming much more the norm, enabling employees to be able to telecommute or for companies to hire a virtual workforce and recruit the top talent they seek without requiring re-location.
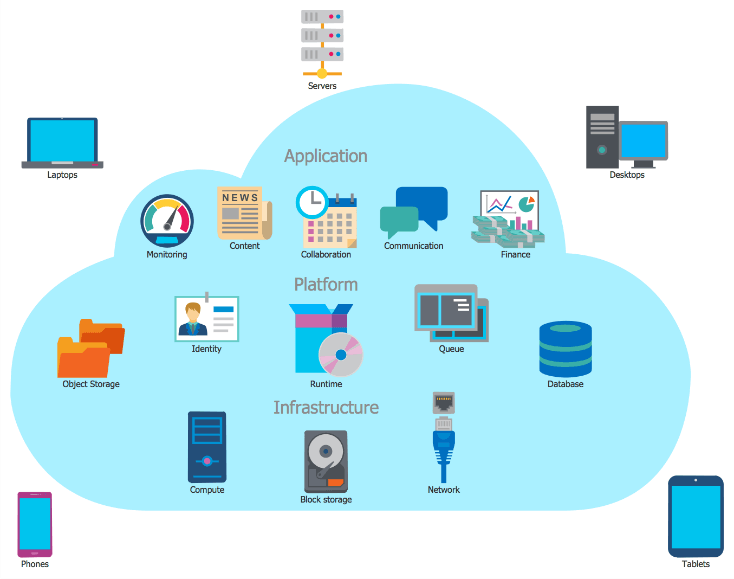
Figure 5:Today's network boundary is hard to define These new technologies provide new applications and methods of communication and data sharing; they often enable all of this over different networking paths such as wireless, or cellular/mobile, and Bluetooth. All of this has compounded the security problem by not only introducing new technologies (and their inherent new vulnerabilities), but more significantly, all of this new technology has diminished the idea of the internal network almost to the point that it does not exist anymore – at least in the classical form. How does network security happen where there is little-to-no defined network perimeter? How do you keep track of authorized and unauthorized users when increasingly users can connect and gain access to the corporate network by numerous methods? In other words, where do you put the perimeter security protections? The main challenge facing organizations today then is to recognize that the focus of network security tools, services, and solutions has been focused on this “fortress” concept of network security, and this has translated to an emphasis on security products designed to secure all the components of the network (the hardware) and to a lesser degree the applications and programs associated with conducting business (the software). The increased complexity of modern networking demands a more strategic and holistic view than traditional (established?) network security can accomplish; what is really required is an entirely different philosophical approach that is more data-centric. That is, the focus should be on what valuable data and information you have along with its value to the organization first, and the other technology-focused strategies should evolve around protecting this valuable data. This data-centric approach to security of your network environment starts with a strategic understanding of what data you have and identifying just how valuable the data is to your operations. This process is commonly known as data classification. Once the data is identified and classified, you must then assess where the data is found in your network, who accesses or “consumes” the data and for what purpose, how the data traverses your network from its origins all the way to when it is no longer required, and how to dispose of the data at the end of its lifecycle. This process is commonly referred to as data flow or business flow analysis. Once you understand what you are trying to protect, perform the data flow analysis to understand where the data is stored or processed and who can or should have access to the data. You can then start to apply the right type of security controls based on an informed understanding of what is at risk. This process is aptly referred to as the risk management model and can be illustrated in a simple formula.
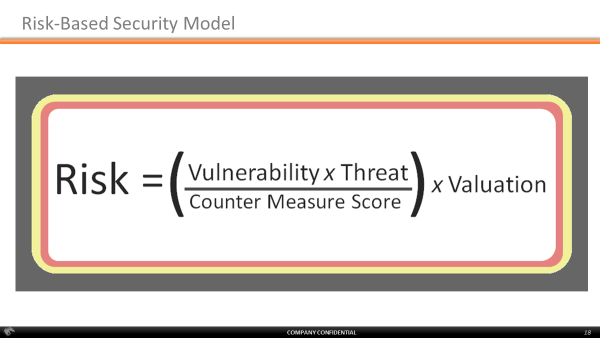
The elements of this simple formula involve the following:
- Risk: the bad thing(s) that could happen that you don’t want to happen such as data loss or theft or letting the wrong people have access to and altering the data
- Vulnerability: weaknesses that are often bugs, coding errors, misconfigurations, features – anything that is wrong with your system or applications that could be exploited to help an attacker do bad things
- Threats: the bad guys and attackers that want to cause you harm. The way in which an attacker can gain access and exploit your network is often considered a threat or sometimes a threat agent. Threats are basically “how” an attacker does their thing – breaking in remotely, physical compromise, phishing campaigns, viruses, or malware
- Countermeasures: basically all of the things you do under the umbrella of security including the deployment of access controls like VPNs or firewalls, intrusion detection systems, alerting and monitoring solutions, file integrity monitoring, whitelisting solutions, and end-point protection
- Valuation: the value of both what it is you are trying to protect and to a lesser degree the cost of the things you do for security
The goal of the risk management model is to reduce risk. Risk is primarily a dollar value – how much is the data that you are trying to protect worth, or what would it cost you to lose it or replace it? The way to reduce risk is some combination of reducing the vulnerabilities in your environment, identifying and blocking or deterring the threats to your environment, and implementing security countermeasures to reduce the effect of any vulnerabilities or threats leftover. You can see elements of the risk-based security model in the security industry today, but the overarching goal or strategy often seems to be missing from the discussion. The new (really old) strategy is to start with knowing what it is you are trying to protect, that is, to have a goal. Once this goal is established, you can develop a strategy that incorporates all of the elements of the risk model but does so in a way that makes sense for your organization and ultimately your security goals. This is an ongoing process, and you must constantly consider changes in technology, in personnel, in the corporate mission, and in the threat landscape. For processes to work on a ongoing basis, they need to be written down, followed, and periodically revised to reflect the latest changes to operations. This approach to security may be referred to as the security life cycle and has the following characteristics:
- Starts with knowing what you’re protecting
- Security requires a systematic approach
- Assess where you are today
- Document where you want to go
- Implement a security architecture
- The policy is the strategy
- The architecture is the coherent, integrated set of tactics by which the policy Is carried out
- Security without policy is simply technology
To completely embrace this approach to security is the most cost-effective manner for applying security to your organization. Chances are you do some of these activities already and have at least some understanding of the risk-based security model as it pertains to your company. What most companies are missing in terms of adopting this security strategy is a reliable sense of what is the data to be protected where the data traverses the existing network and what systems are involved in the processing and storage of the data. A necessary first (or remedial) step is to discover exactly what is going on in your network.
Discovery is Key
The need to understand where your network extends and what systems are either attached or attempting to attach to your network has never been more urgent. This discovery must happen on a continuous basis. Technological advances require technological solutions, but they are much more effective if implemented with an overall data security strategy rather than attempting to provide “fortress-like” protection of the enterprise network. This discovery needs to include at least the following:
- WHO
- Users
- Administrators
- Developers
- Contractors
- Guests
- Customers
- WHAT
- Workstations
- Laptops
- Appliances
- Rogue Devices
- Internet of Things (IoT)
- BYOD (mobile, tablets)
- WHERE
- Wired networks (WAN, LAN)
- Virtual networks (vLANs)
- Wireless networks
- Cellular networks
- Bluetooth
- NFC, RFID, etc.
There is an ongoing need to have detection capabilities that can detect users and devices that are already attached to the network or that are trying to gain access to the corporate network.
How Do You Do Discovery Today?
Discovering what is on your network is one of the most fundamental steps in securing a company's network, data, and critical business systems. However, getting a good handle on the authorized devices that should be on your network and unauthorized stuff that shouldn't be remains a significant challenge for most security teams. Limited security staff, distributed networks, and diverse network infrastructures are just a few of the challenges teams face. There are numerous tools and “solutions” on the market today that endeavor to help you toward this goal. They are often categorized under “continuous monitoring”, “network discovery” tools. But before you go investing the big bucks in a solution, make sure you understand and document the goals and processes that the tool will help you accomplish. This is key. Once you have a solid understanding of what is on your network, you can continuously monitor those devices for security vulnerabilities, insecure configurations, connections to untrusted networks or devices, and device-based attacks.
Final Thoughts
The concept of fortress or perimeter-based security for network security is largely obsolete these days. Effective security requires that you have a goal or strategy in mind, namely, to protect the information and data that is the lifeblood of your organization. Protecting the data requires an understanding of where the data resides, who accesses it, and where it is passed around and consumed. Once your data security strategy is determined, you must understand the very nature of your corporate environment at a system- or asset-level. This must be done on an ongoing basis to support the ongoing nature of the security cycle.

About the Author: Jeff Man is a respected Information Security expert, adviser, and evangelist. He has over 33 years of experience working in all aspects of computer, network, and information security, including risk management, vulnerability analysis, compliance assessment, forensic analysis and penetration testing. He has held security research, management and product development roles with NSA, the DoD and private-sector enterprises and was part of the first penetration testing "red team" at NSA. For the past twenty years, he has been a pen tester, security architect, consultant, QSA, and PCI SME, providing consulting and advisory services to many of the nation's best known brands. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

