
The MuddyWater threat attack group is using a spam campaign to hijack victims' computers and steal sensitive information. Discovered by Heimdal Security in early April, the campaign begins when malicious actors use social engineering techniques to trick a user into opening a malicious Microsoft Office document attached to a phishing email. The document contains VBA macro code which, if enabled, uses the Windows scripting host “//E” command line to drop a Base64 encoded payload. This payload communicates with a command-and-control server to collect sensitive information including files from multiple folders and subsequently exfiltrate that data. As part of the campaign, MuddyWater is using WebRequest.GetSystemWebProxy as part of their efforts to obtain remote control over the infected machine. Digital attackers then use their stolen access to restart a user's machines and modify the registry keys with an "Update Service" message.
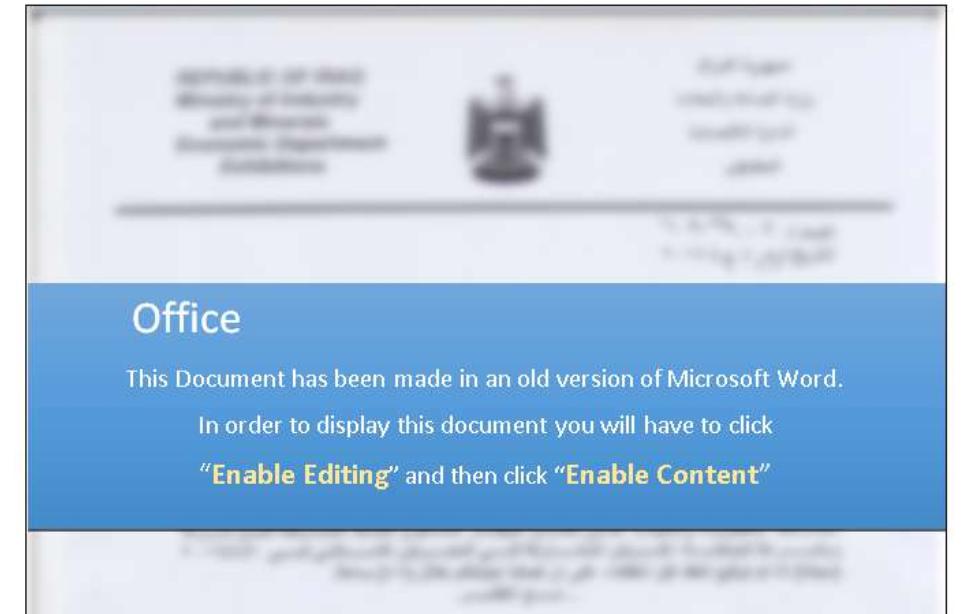
A screenshot of one of the malicious documents. (Source: Heimdal Security) This campaign isn't MuddyWater's first operation. Back in 2017, Palo Alto Networks disclosed how the threat actor had staged a series of targeted attacks against Middle East nations including Saudi Arabia, Iraq and Iran between February 2017 and October 2017. Other security companies that picked up on the attacks originally attributed the malicious activity to FIN7, another threat actor group. But Palo Alto Networks found in its own research that FIN7 wasn't the most likely candidate. As a result, the firm nicknamed the attackers "MuddyWater" due to the difficulties associated with attributing them. The attack detected by Heimdal Security indicates the longevity which many bad actors such as MuddyWater tend to enjoy. It also demonstrates these malefactors' ongoing commitment to launching digital attacks against users. Acknowledging this reality, organizations would be wise to use this attack as an opportunity for teaching their employees about social-based threats. They can begin this effort by creating a security awareness program (or modifying an existing platform) to educate their employees about phishing attacks.

