
A data breach known as "Collection #1" exposed approximately 800 million email addresses as well as tens of millions of passwords. In the beginning of January, multiple people reached out to Australian web security expert Troy Hunt about a sizable collection of files hosted on cloud service MEGA. This collection, which is no longer available on MEGA, consisted of 12,000 separate files containing a total of more than 87 GB of data. One of the individuals who contacted Hunt informed him that members of a popular hacking forum were spreading the word about the leaked information. Some of them even shared an image of the leak's root folder, which is named "Collection #1." Hence the name for this data breach.
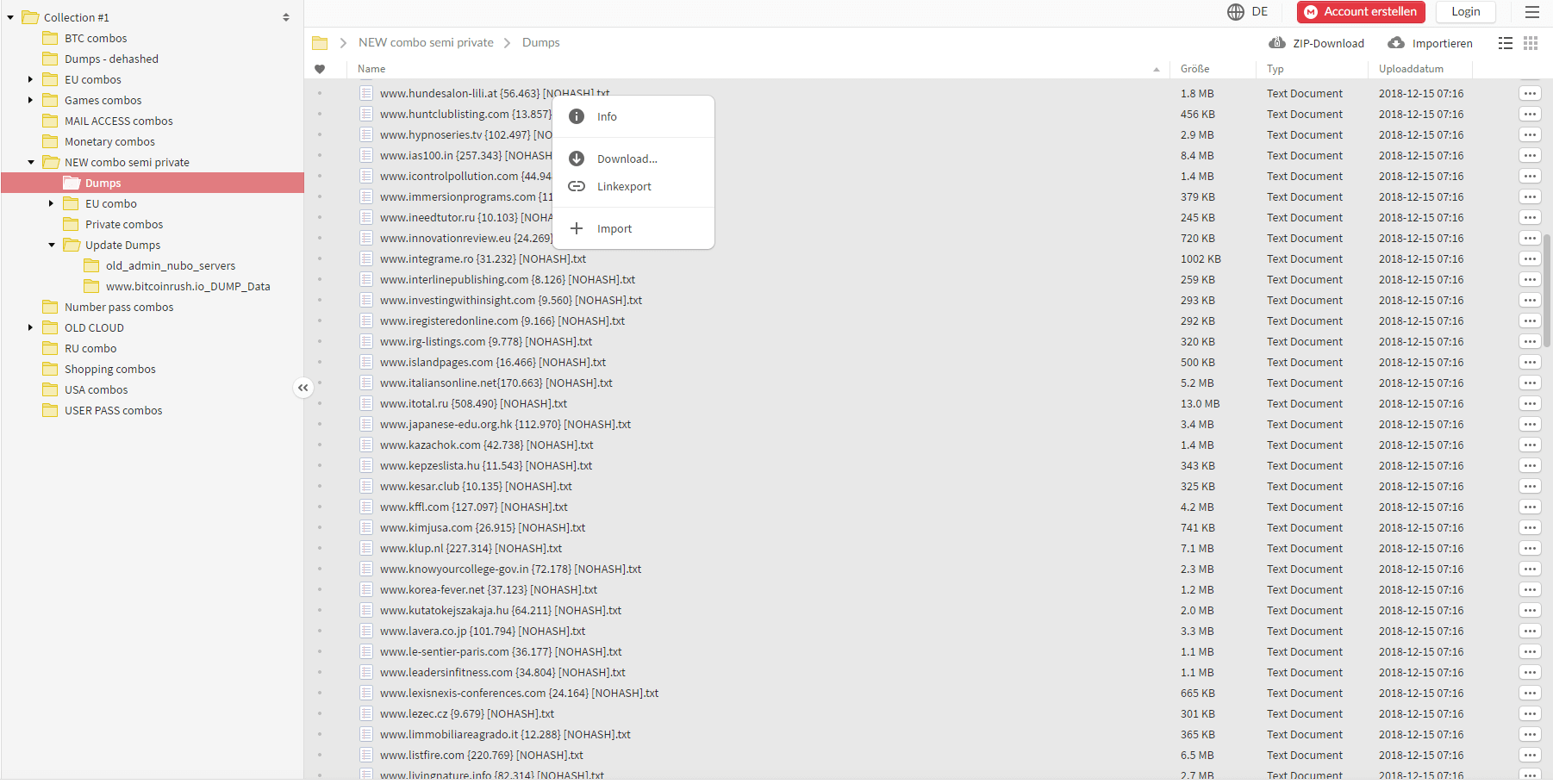
A screenshot of the "Collection #1" root folder. (Source: Troy Hunt) In his analysis of the "collection of 2000+ dehashed databases and Combos stored by topic" contained in the root folder, Hunt found 2,692,818,238 rows made up of email addresses and passwords. A little less than half (1,160,253,228) were unique combinations. Digging down even further, Hunt discovered 772,904,991 unique email addresses and 21,222,975 unique passwords. This data dump is larger than the majority of security incidents disclosed thus far. But there are a few that stand toe-to-toe with it. In October 2018, for instance, Yahoo agreed to pay $50 million as part of a settlement for a 2013 data breach that exposed all three billion of the web service's accounts. Though "Collection #1" derives its leaked information from a number of sources, Hunt decided to upload the dumped files to his Have I Been Pwned (HIBP) service. He did so partly because some 140 million email addresses and over 10 million passwords were new to HIBP. Adding that data could help users discover if they've been breached and compare their passwords to Hunt's Pwned Passwords feature. The security researcher said that the publicity the data breach was receiving on the hacking forum also factored into his decision. As he wrote in a blog post:
The data was also in broad circulation based on the number of people that contacted me privately about it and the fact that it was published to a well-known public forum. In terms of the risk this presents, more people with the data obviously increases the likelihood that it'll be used for malicious purposes.
Users are encouraged to use Have I Been Pwned and Pwned Passwords to check if their account credentials have been breached. Going forward, they should also use these expert tips to create a strong, unique password for each of their web accounts. They might consider storing those passwords using a password manager and activating two-factor authentication (2FA) for added protection wherever they can.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

