
A survey revealed that approximately half of employees didn't know how to respond in the event their organization suffered a ransomware infection. In its survey of North American business employees, Kaspersky found that 45% of respondents overall did not know the proper steps they should take in response to a ransomware attack. Respondents whose employer had suffered a crypto-malware infection weren't significantly more knowledgeable about what to do. Just 40% said they knew what steps to take. That's almost the same ratio of employees (37%) who failed to provide Kaspersky with an accurate definition for ransomware. These findings are a concern given an earlier study conducted by Kaspersky. This research showed that ransomware struck at least 900,000 users every six months and that a successful infection cost victims more than $1 million on average.
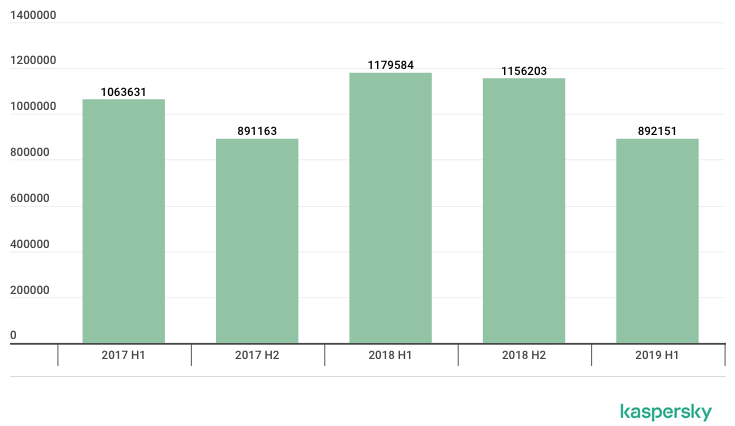
Number of users attacked with ransomware, H1 2017-H1 2019 (Source: Kaspersky) Organizations can't afford to not know what to do in response to a ransomware infection. So, what are they supposed to do if crypto-malware strikes them? Brian Bartholomew, principal security researcher for the Global Research and Analysis Team at Kaspersky North America, explained that organizations should never pay the ransom:
First, paying a ransom will never guarantee that all of your data will be returned – it might be partially returned or not at all. There is also no way to tell if your information has been sold in underground markets once obtained. Second, paying a ransom only encourages cybercriminals to further carry out these attacks as they are one of the most financially profitable attacks malefactors can perform.
Instead, organizations should implement security measures that can help them prevent a ransomware infection in the first place. These guidelines include using security awareness training to educate their employees about some of the most common types of phishing scams and email attacks in circulation today. They should also invest in a tool such as Tripwire File Analysis for the purpose of monitoring for suspicious file behavior.

