
A newly discovered ransomware family called "Nefilim" told its victims that it would publish their stolen data within a week unless they paid their ransom. According to Bleeping Computer, Nefilim started up near the end of February 2020. The threat attracted the attention of security researchers because it shared much of the same code with version 2.5 of Nemty, another ransomware family. Unlike Nemty, however, Nefilim arrived without a ransomware-as-a-service (RaaS) component and instructed victims to use email communications, not a website accessible via Tor, to receive payment instructions. Nefilim's method of distribution was unknown at the time of writing, but Bleeping Computer reported that the ransomware was likely abusing Remote Desktop Services. Upon a successful infection, the ransomware leveraged AES-128 encryption to run its encryption routine. It then appended the .NEFILIM extension to the name of every file it had affected before dropping its ransom note "NEFILIM-DECRYPT.txt."
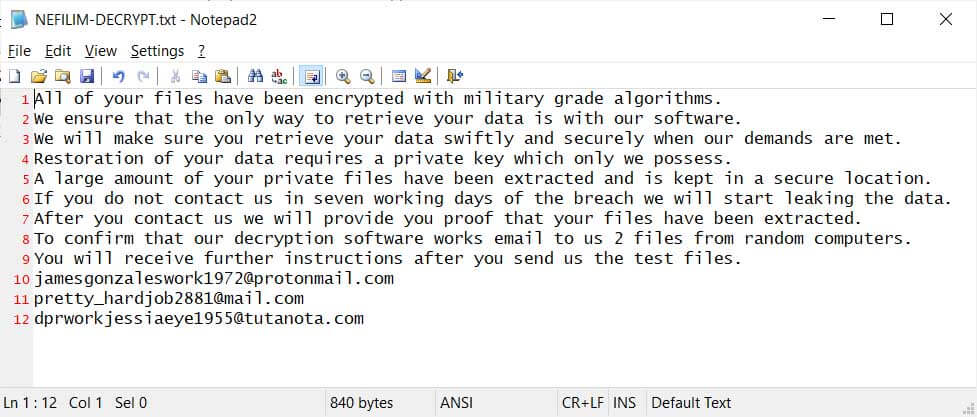
Nefilim's ransom note (Source: Bleeping Computer) Part of this message informed victims that the ransomware would leak their data if they did not pay their ransom within seven days. As quoted by Bleeping Computer:
A large amount of your private files have been extracted and is kept in a secure location. If you do not contact us in seven working days of the breach we will start leaking the data. After you contact us we will provide you proof that your files have been extracted.
At the time of writing, security researchers had not identified a weaknesses that they could leverage to develop a free decryption tool. The emergence of Nefilim highlights the need for organizations to protect themselves against a ransomware attack. That's especially the case given the fact that Nefilim isn't the first crypto-malware family that's threatened to publish non-compliant victims' data. With that in mind, organizations should endeavor to prevent a ransomware infection in the first place using these best practices.

