
Some new variants of the Agent Tesla infostealer family are capable of stealing data from multiple VPN clients and web browsers. SentinelOne observed that attackers continue to deploy Agent Tesla across various stages of their operations, as this malware enables criminals with even low levels of technical expertise to manipulate and manage their victims' infected devices. To keep up with attackers' evolving demands, the authors of Agent Tesla have made a habit of updating their creation with new functionality. The security firm revealed in its research that one of these changes helped to broaden the list of software targeted by the malware:
Agent Tesla is now able to harvest configuration data and credentials from a number of common VPN clients, FTP and Email clients, and Web Browsers. The malware has the ability to extract credentials from the registry as well as related configuration or support files.
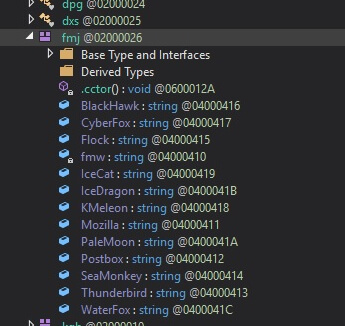
A view of some of the software programs targeted by Agent Tesla's new variants. (Source: SentinelOne)
Overall, SentinelOne found that the threat was capable of targeting 55 software programs at the time of analysis including Apple Safari, Google Chrome, OpenVPN and Yandex.
The malware ultimately sent this harvested information to the attackers' command-and-control (C&C) server. Depending on its internal configuration, the threat completed this transmission using either SMTP or FTP.
This wasn't the first time that Agent Tesla made news in 2020. Back in February, for instance, news emerged of a spam campaign that had leveraged malicious RTF documents to distribute notorious infostealers including Agent Tesla and Lokibot. That was less than three months before the security community learned of digital attackers having used spearphishing campaigns to target oil and gas companies with samples of the AgentTesla infostealer family.
This threat activity highlights the need for organizations to defend themselves against a malware infection by examining suspicious files in quarantined environments. Learn how Tripwire File Analyzer can help in this regard.

