
Security researchers came across a new ransomware family called "CryCryptor" that masqueraded as a Canadian COVID-19 tracing app. CryCryptor emerged just days after the Canadian government announced it would support the development of a national, voluntary tracing app for COVID-19 called "COVID Alert." That official app had not yet entered its testing phase in Ontario at the time of this writing. ESET analyzed CryCryptor and found that the threat was based on CryDroid, a form of "Android Ransomware source code for researchers" which was available on GitHub. As if educational ransomware strains have ever worked out before. In this particular case, CryCryptor capitalized on successful installation by requesting the permission to access files on the infected device. It then abused that right to encrypt files on external media with certain extensions using AES. This process led the ransomware to append ".enc" to each file it had affected as well as to generate a unique salt (ending in "enc.salt") along with an initialization vector ("enc.iv") for each encrypted file. Meanwhile, the crypto-malware removed the original file from the infected computer. It's then that the threat displayed its ransom note.
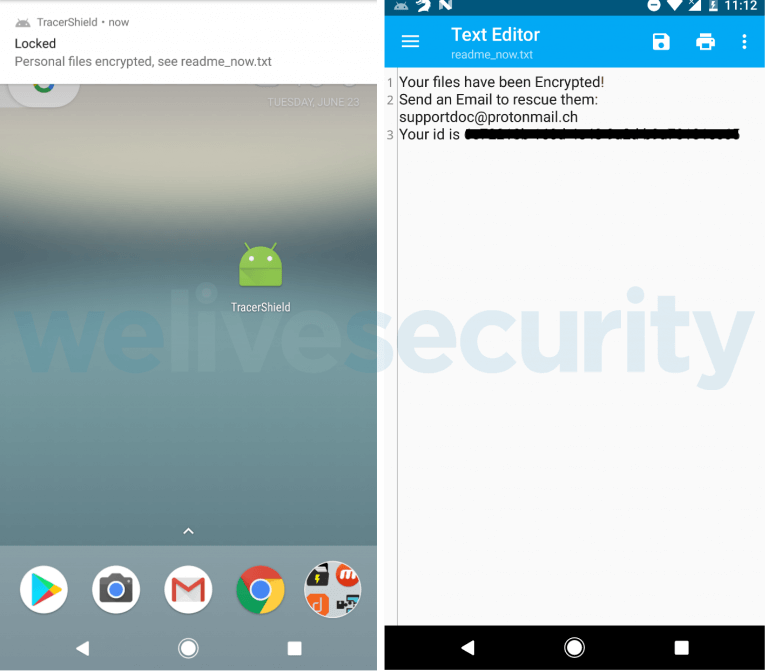
File encryption notification (left) and contents of the readme_now.txt file (right). (Source: ESET) Fortunately, the Slovakian security firm was able to develop a decryption tool that enabled victims of CryCryptor to recover their files for free. ESET's researchers described how they were able to do this:
The service responsible for file decryption in CryCryptor has the encryption key stored in shared preferences, meaning it doesn’t have to contact any C&C to retrieve it. Importantly, the service is exported without any restriction in the Android Manifest (security weakness CWE-926), which means it is possible to launch it externally.
ESET explained that it notified Canadian Centre for Cyber Security about the ransomware threat as soon as it discovered it. It also notified GitHub about the risks involving CryDroid.

