
Security researchers have released a new decryption tool that could help victims of Jigsaw ransomware recover their affected files for free. In a blog post announcing the new utility, Emsisoft explained that its decryptor can work against 85 extensions employed by the ransomware family. The security firm also said that they would update their tool to support additional extensions in the future.
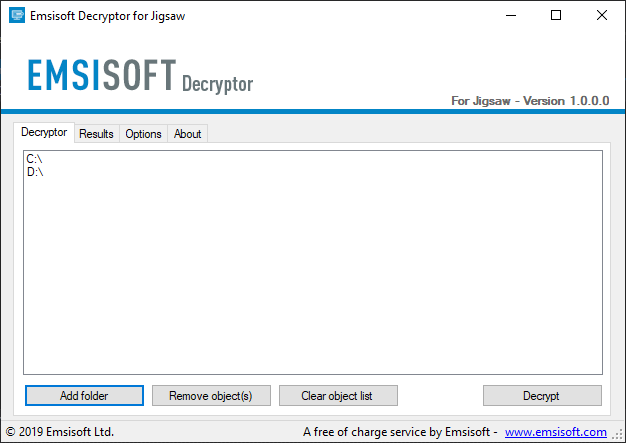
Emsisoft's decryptor for Jigsaw ransomware As noted by Emsisoft, the first variant of Jigsaw ransomware appeared in 2016 and masqueraded as a Firefox or Dropbox update. Its GUI featured an image of "Billy the Puppet" from the "Saw" movies, whose main antagonist goes by the name "Jigsaw." Digital criminals could initially access Jigsaw only by purchasing it on a Tor marketplace. But its malware authors ultimately made their creation open source. This decision enabled malicious actors to develop their own variants that were capable of foiling a decryptor released in 2016. Jigsaw ransomware stands out for using its ransom note to inform victims that it will delete one of their files an hour after it's completed its encryption routine. The message goes on to explain that the rate of data loss will increase exponentially from there. After 72 hours, Jigsaw will delete all of a victim's remaining data, its note reveals. The crypto-malware also threatens to delete 1,000 files as a form of punishment if a user attempts to stop Jigsaw's processes or reboot their infected machine.
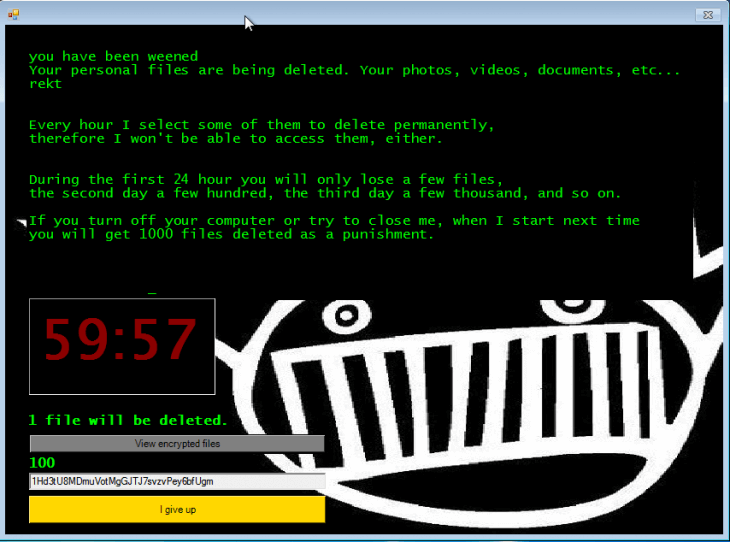
A ransom note used by Jigsaw ransomware. (Source: Emsisoft) Users should try using Emsisoft's decryption utility in the event they suffer a Jigsaw ransomware infection. Given digital criminals' commitment to create new variants, however, users would be wise to take some additional steps to protect themselves. In particular, they should endeavor to prevent a ransomware infection in the first place by keeping their machines' software up-to-date and exercising caution around suspicious email attachments. Additional ransomware prevention recommendations can be found here.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

