
Researchers discovered a new variant of the MegaCortex ransomware family that changes a victim's Windows password upon execution. Discovered by MalwareHunterTeam and reverse engineered by Vitali Kremez, the threat seized the attention of Bleeping Computer when its ransom note stated that "All of your user credentials have been changed and your files have been encrypted." The computer self help site worked with Kremez to confirm this activity. Together, they found that the ransomware variant executed the net user command upon execution to change a victim's password. This capability explains why the threat displayed a "Locked by MegaCortex" notice before a victim even has a chance to log in.
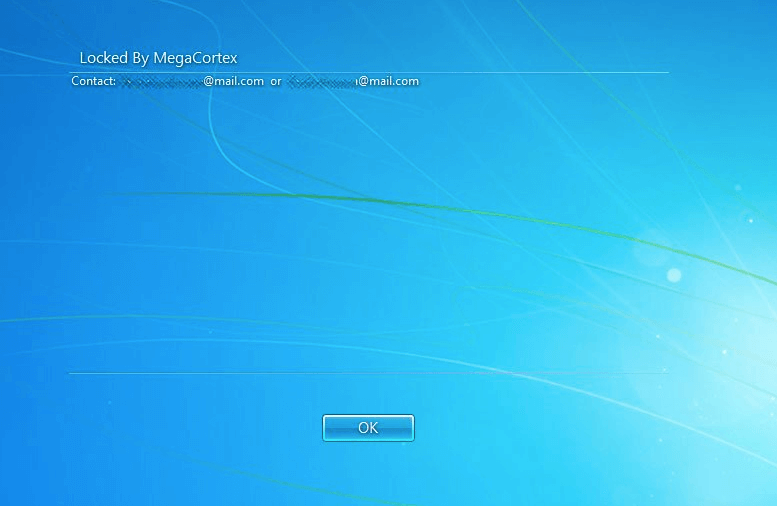
The "Locked by MegaCortex" notice (Source: Bleeping Computer) The ransom note made another significant claim about the variant's capabilities. Indeed, the following portion drew Bleeping Computer in:
We have also downloaded your data to a secure location. In the unfortunate event of us not coming to an agreement we will have no choice but to make this data public. Once the transaction is finalized all of copies of data we have downloaded will be erased.
Researchers investigated this claim and were unable to confirm its legitimacy. But they weren't able to rule out the feature, either. In response, victims of the ransomware might want to ask that those responsible for their infection prove they actually have their data. This isn't the first time that MegaCortex has appeared in the news. Back in July, the ransomware's handlers asked victims in one of their variant's ransom notes to not “waste our and your time” and to remember that they “don’t do charity.” Not long thereafter, a new variant emerged sporting a variety of anti-analysis capabilities. MegaCortex's ongoing evolution highlights the need for organizations to defend against ransomware. Specifically, they should use these steps to prevent a crypto-malware infection in the first place.

