
A new version of the Mount Locker crypto-ransomware strain is specifically targeting victims' TurboTax files.
As reported by Bleeping Computer, Advanced Intel's Vitali Kremez came across a new Mount Locker sample that specifically sought out files used by the TurboTax tax preparation software.
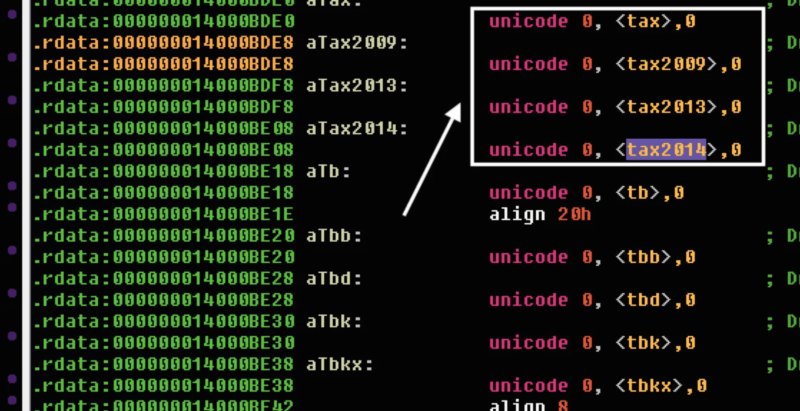
In particular, Kremez observed the sample going after files bearing the ".tax," ".tax2009," ".tax2013" and ".tax2014" extensions.
The ransomware isn't restricting its sights to just those four file extensions, however. As quoted by the computer self-help site:
While Mount Locker is oddly targeting file extensions for specific tax years, Kremez told BleepingComputer that the 'tax' targeting would match all extensions that contain the string.
This wasn't the first time that Mount Locker made news in 2020.
Back in September, for instance, those responsible for maintaining the ransomware attracted the attention of the security community for demanding ransom payments in the millions of dollars.
In one case, the Mount Locker gang asked for $2 million after claiming to have stolen 400 GB from a victim.
The malicious actors threatened to make that stolen information public if the victim refused to pay the ransom.
More and more ransomware attacks are incorporating at least the threat of data theft into their attack chains. In its Quarterly Ransomware Report for Q3 2020, for instance, Coveware found that nearly half of all successful ransomware attacks had threatened to release exfiltrated data during those months.
The security firm also learned that several ransomware families had in some cases not honored the ransom payments made by victims to prevent the attackers from publishing their data online.
This reality highlights the need for organizations to defend themselves against a ransomware attack. One of the best ways they can do that is by working to prevent a ransomware infection from occurring in the first place. This resource is a good place to start.

