
A new wiper malware falsely informed victims in its infection notice that two security researchers had been responsible for attacking them. According to Bleeping Computer, users who downloaded programs from free software and crack sites found that they couldn't successfully authenticate themselves and unlock their Windows computers. Instead, their machines displayed an infection notice informing them that Vitali Kremez and MalwareHunterTeam, two well-known security researchers, had infected their computers. This note then instructed them to reach out to those individuals to restore access to their computers.
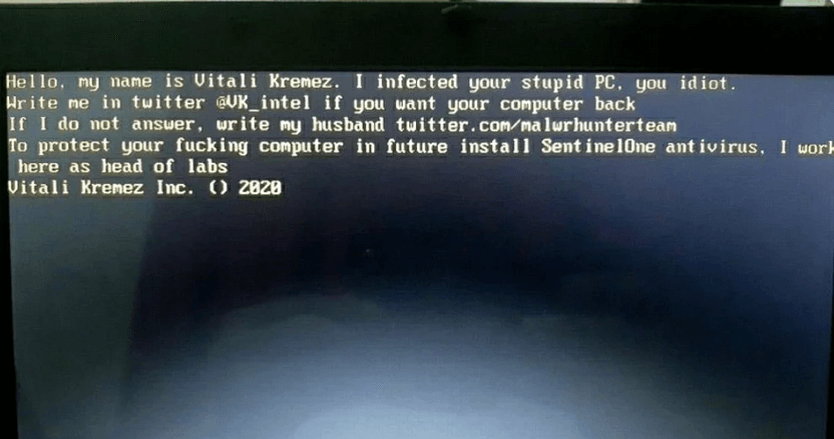
MBR locker impersonating Vitali and MalwareHunterTeam (Source: Bleeping Computer)
Hello, my name is Vitali Kremez. I infected your stupid PC. you idiot. Write me in twitter @VK_intel if you want your computer back If I do not answer, write my husband twitter.com/malwrhunterteam To protect your ***ing computer in future install SentinelOne antivirus. I work here as head of labs. Vitali Kremez Inc. () 2020
Neither of these researchers had anything to do with this malware attack. The same can be said for "SentinelOne Labs Ransomware." In contrast to the threat described above, this attack's note disclosed Kremez's email addresses and phone number for the purpose of victims reaching out to him. Both threats were similar in that they replaced the master boot records (MBRs) on victims' computers. Employed by other malicious campaigns such as ZeroCleare, this technique wiped the infected computer by preventing it from finding the information it needed to successfully boot the OS upon startup. There's hope for victims, however. Bleeping Computer noted that digital attackers used a publicly available tool to create numerous "MBRLockers" at the beginning of 2020. Threats that used this tool created a backup of a victim's original MBR and stored it on their computer before replacing it. That means it's possible for users to restore access to their computers. At the time of writing, Bleeping Computer had not confirmed whether the MBRLockers that blamed Vitali Kremez and MalwareHunterTeam for the infections had used that same tool.

