
Security researchers came across a series of odd protest-themed spam email messages that appeared to target the Atlanta Police Foundation. SANS' Internet Storm Center observed that the spam messages first appeared to be instances of an extortion scam campaign. With "Crime Research Center" as the sender, the emails claimed in their messages that recipients needed to pay a penalty as a result of a shooting that they allegedly committed at a protest. The emails then provided them with a link through which users could pay a fine.
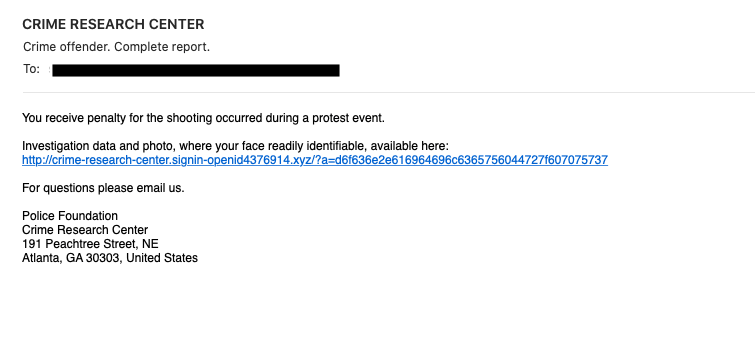
Screenshot of one of the attack emails. (Source: SANS' Internet Storm Center) In terms of red flags, each of the emails suffered from poor grammar and nonsensical logic. (It's not standard for law enforcement authorities to dismiss a shooting with a monetary penalty. Also, any type of criminal fine would also not originate from an organization such as the Atlanta Police Foundation, an entity which works to enhance the Atlanta Police Department's effectiveness but which does not itself actively enforce the law.) Clicking on the embedded link led users to a page that presented them with fictitious incident number, customer number and email address surrounding their alleged crime. It then instructed them to click a "Downloadable Printable Copy." Doing so redirected them to a legitimate page employed by the Atlanta Police Foundation. In its analysis, SANS' Internet Storm Center reasoned that browser fingerprinting, IP address checks or chance might have prevented its researchers from viewing the final scam page. The security team reasoned there could have been another motivation at work, as well. As quoted in their research:
...[M]aybe someone is just trying to cause a "Layer 8" (human) denial of service against the Atlanta Police Foundation. With many recipients receiving an obviously fraudulent message leading to a donation form, they may report it as fake (that was my initial gut feeling) and cause the donation form to be shut down. This is currently my "most likely" explanation.
News of this spam campaign arrived just days after security researchers came across an attack email that leveraged a fake Black Lives Matter voting campaign to distribute Trickbot malware.

