
I've added some handy tools to my pentest toolbox this year. You'll find a short description of each with links to more information below. Whether red or blue team, you'll want to know what these tools can do.
Password Spraying
Password spraying is guessing a few passwords against a large list of users in order to avoid account lockout. You would be surprised at how many users pick “Fall2016” or whatever the current season and year are as their password. On an external assessment, it is great fun to do a password spray against Outlook Web App (OWA), and MailSniper by Beau Bullock will help you do it. It makes password spraying OWA a breeze and has many other features for downloading the entire address book, as well as searching multiple inboxes for sensitive information. Once you get creds, try a malicious outlook rule for thrillz. It works! If you have internal access and want to password spray domain users, it doesn’t get any easier than using this PowerShell script. Thanks, Beau!
Bloodhound
Bloodhound is a tool for understanding the relationships and resources in an Active Directory domain. It's very useful for finding critical resources that will help you pivot through an internal network. Check out the BsidesLV presentation here and more information on usage here.
Powershell Without Powershell
This is an excellent option for bypassing client antivirus and application whitelisting restrictions. Brian Fehrman has a great write-up here on this technique. I just used this method last week on a Pivot test for the win. Thanks, Brian.
Grabbing Creds From a Locked Windows Machine
Mubix had a great post in September about plugging in a USB device and grabbing password hashes from a locked windows machine. The USB device acts like an ethernet adapter and is automatically installed by Windows. Since then, a new module “QuickCreds” has been released for the LAN turtle, so this attack is as easy as buying the $50 LAN Turtle and enabling the QuickCreds module. Fun stuff!
Egress Checker
Attackers on an internal network are going to want to exfiltrate information. To do this, they will be looking for a port that is open out of the internal network that can be used to send data or establish a Command and Control session. The website http://allports.exposed is a quick way to check if a particular port is open. Simply add a colon (:) followed by the port number you are interested in checking to the URL. If the text “Open Port” is received, then the port is open. I used a PowerShell script similar to the one documented here to check many ports at once to see how open the internal network is for egress.
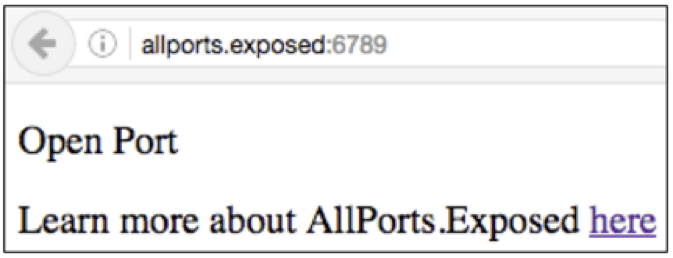
Allports.Exposed Egress Checker
LuckyStrike
Doing some phishing? This little gem will crank out the Macro enabled Microsoft Office Documents for you in neat and effective ways. If you do phishing often, the LuckyStrike tool will be a welcome addition.
Reconnaissance with Censys
Censys is a search engine for finding internet resources that exist in a particular IP range belonging to a particular company and more. This tool is helpful when you are mapping out the attack surface for a given company. Check it out here. Try some of these out and see just how easy hacking can be!

About the Author: Carrie Roberts is a Security Analyst at Black Hills Information Security (BHIS), and regularly posts to the BHIS blog at http://www.blackhillsinfosec.com/?page_id=2156. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.

