
Security researchers observed that digital attackers are increasingly incorporating the reCaptcha API into their phishing campaigns. Barracuda Networks explained that malicious actors are starting to outfit their phishing attempts with reCaptcha walls so that they can shield their landing pages from automated URL analysis tools as well as add a sense of legitimacy to their operations. Some of these efforts have consisted of deploying a fake checkbox and form. Yet the security firm revealed that it's increasingly seeing fewer fake reCaptcha boxes as attackers continue to embrace the actual API. Indeed, it spotted just one fake box compared to 100,000 phishing emails using the real deal. That's not all it found. Barracuda Networks revealed that it had discovered a campaign consisting of no less than 128,000 attack emails. All of those messages informed recipients that they had a voicemail awaiting them and that they could access a recording of it by clicking on an attachment. Once clicked, that HTML file redirected recipients to a page that contained only the reCaptcha wall.
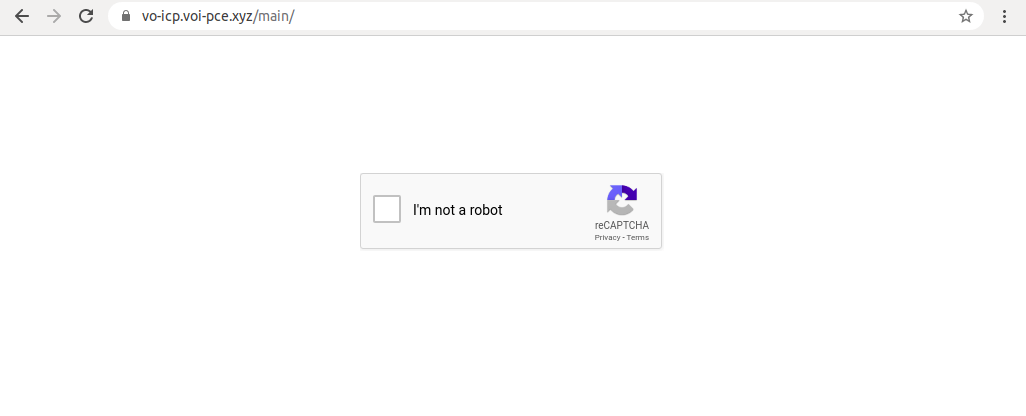
The reCaptcha wall that digital attackers had incorporated into their phishing campaign. (Source: Barracuda Networks) The security firm explained what happened after a user completed the reCaptcha challenge:
Once the user solves the reCaptcha in this campaign, they are redirected to the actual phishing page, which spoofs the appearance of a common Microsoft login page. It is not clear whether the page’s appearance matches the user’s legitimate mail server, but it’s possible that using some simple reconnaissance the attacker could find this sort of information to make the phishing page even more convincing.
The growing prevalence of reCaptcha walls in phishing campaigns highlights the need for organizations to defend themselves against more advanced email attacks. One of the ways they can do this is by educating their employees about the latest attack types and techniques employed by phishers today. This resource is a great place for them to start.

