
Phishers are leveraging Google Translate in their attempts to steal the login credentials for users' Google and Facebook accounts. Larry Cashdollar, a member of Akamai's Security Intelligence Response Team (SIRT), received an email in early 2019 informing him that someone had accessed his Google account from a new Windows device. On his phone, the email looked relatively convincing in its condensed state. But examining the email on his laptop confirmed his suspicions: the email was fake and had originated from the suspicious sending address "facebook_secur@hotmail[dot]com."
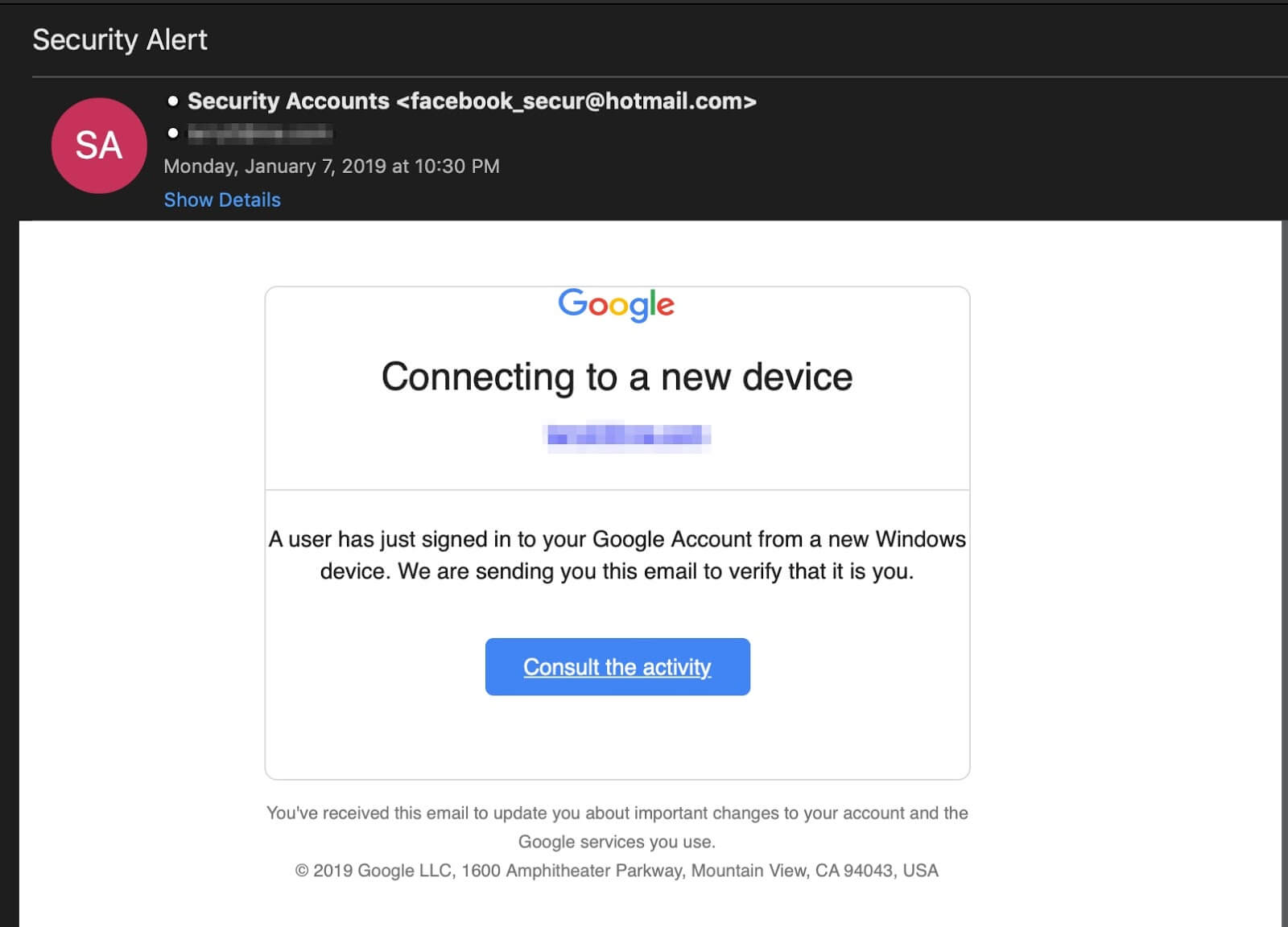
A screenshot of the phishing email received by Cashdollar. (Source: Akamai) Curious, Cashdollar clicked on the "Consult the activity" button provided in the email. He found himself redirected to a fake Google login page. What made this page stand out is that the digital attackers had used Google Translate to load the malicious domain while displaying a legitimate Google domain in the address bar. It's possible this tactic could trick some computer users into supplying their Google login credentials. Even so, others would see the "mediacity" domain being translated and then recognize the login page as a fake.
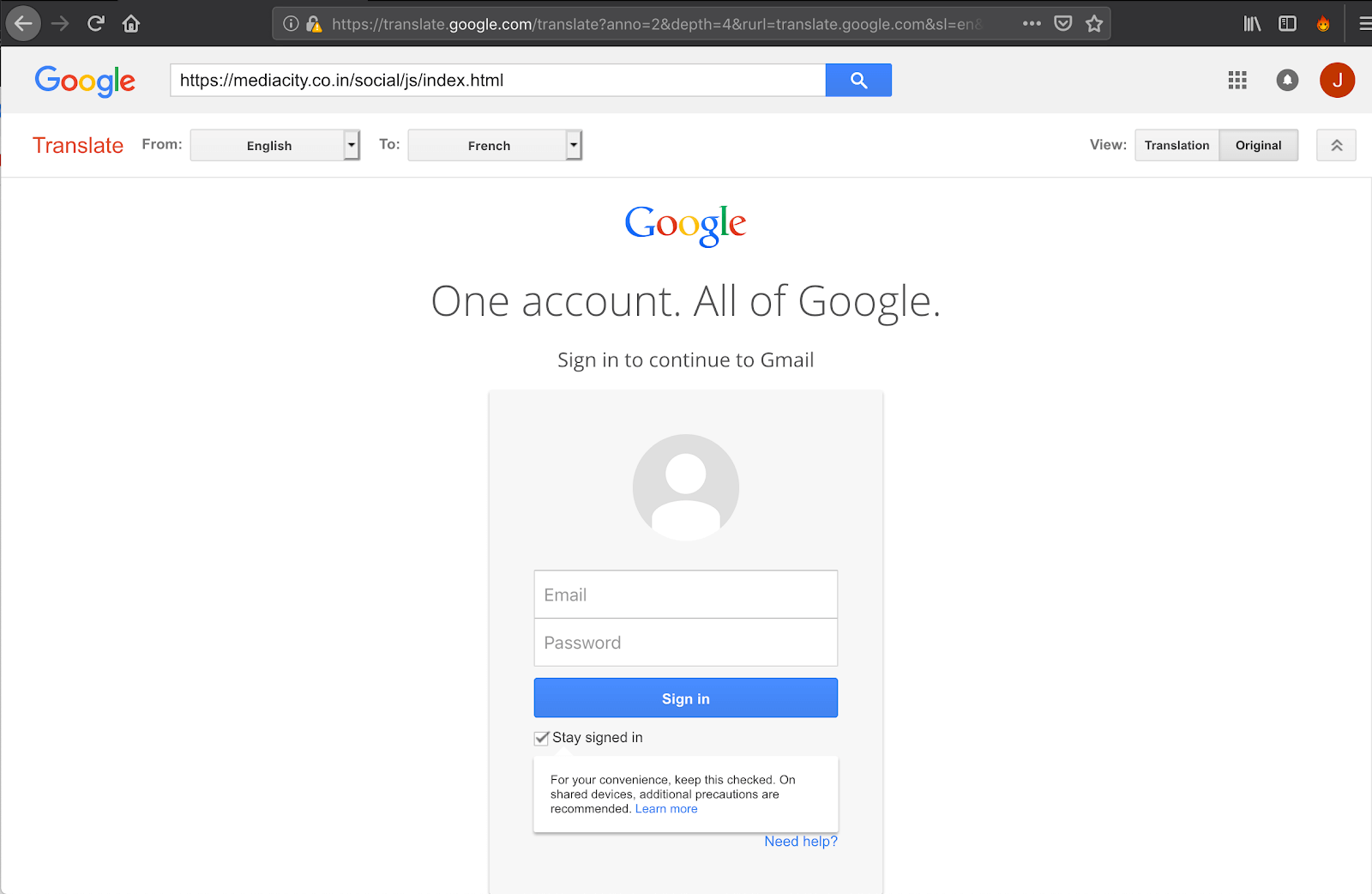
The phishing attack's landing page, as loaded through Google Translate. (Source: Akamai) If a user did supply their Google account credentials, they immediately found themselves to be the subject of a second phishing attack designed to steal their Facebook credentials. These back-to-back attacks make the campaign unique, as Cashdollar explains in a blog post:
It isn't every day that you see a phishing attack leverage Google Translate as a means of adding legitimacy and obfuscation on a mobile device. But it's highly uncommon to see such an attack target two brands in the same session. One interesting side note relates to the person driving these attacks, or at the least the author of the Facebook landing page - they linked it to their actual Facebook account, which is where the victim will land should they fall for the scam.
Users can protect themselves against these innovative scams by familiarizing themselves with the most common types of phishing attacks. They should also enable two-factor authentication (2FA) whenever and wherever they can.

