
Fraudsters launched a new phishing attack in which they sent out a fake cPanel advisory warning recipients about fabricated security vulnerabilities. On August 5, cPanel and WebHost Manager (WHM) users began reporting of having received a fake advisory that appeared to have originated from the company. The fake advisory informed recipients that cPanel had released new builds to address a series of security vulnerabilities affecting cPanel and WHM installations 88.0.3+, 86.0.21+ and 78.0.49+. To add a sense of legitimacy, the attackers incorporated cPanel's logo into their email. But they didn't stop there. As Bleeping Computer noted in its coverage of the attack:
In addition to a well-worded email with little or no grammar and spelling issues, the threat actors used language commonly found in security advisories. The attackers registered the domain 'cpanel7831.com' to make the scam appear as an authentic advisory from cPanel and are using Amazon Simple Email Service (SES) to send out the emails.
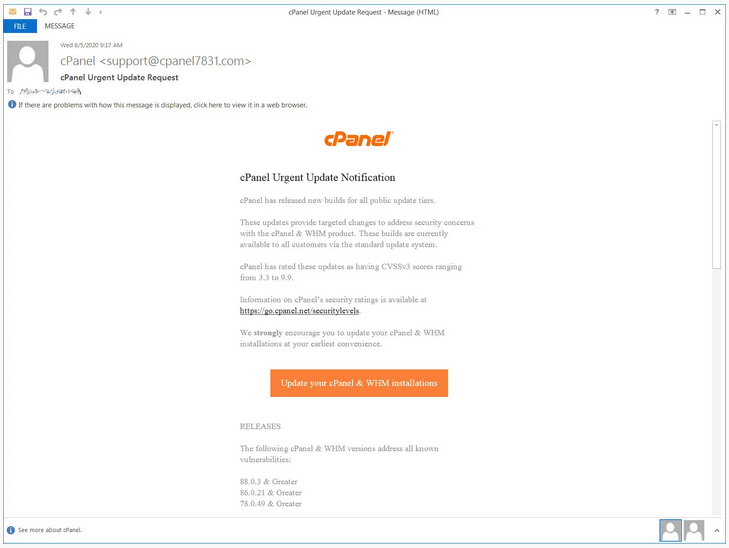
Screenshot of the fake cPanel advisory (Source: Bleeping Computer) In the event that a user clicked on the email's "Update your cPanel & WHM installations" button, they found themselves redirected to a website that prompted them to authenticate themselves using their account credentials. That phishing landing page was down at the time of Bleeping Computer's analysis and instead redirected to a Google keyword search for "cpanel." If anyone fell for the phishing attack described above, they should log into their accounts and change their passwords as soon as possible. In the meantime, organizations should use ongoing security awareness training to strengthen their users' defenses against similar types of phishing attacks. They can do so by educating their users about some of the most common types of campaigns that are in circulation today and following that training up with ongoing phishing simulations. This resource serves as a good place to start.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

