
Digital fraudsters are stealing Microsoft Office 365 administrator credentials as part of a broader phishing campaign targeting organizations. The campaign began with a phishing email that leveraged Microsoft and its Office 365 brand to lull recipients into a false sense of security. This attack email was unique, however, in that it originated from validated domains that don't belong to Microsoft. PhishLabs says this tactic gives attackers an advantage:
This is beneficial for attackers because many email filtering solutions leverage the reputation of a sender domain as a major component of determining whether to block an email. Well established domains with a track record of sending benign messages are less likely to be quickly blocked by these systems. This increases the deliverability and efficiency of phishing lures.
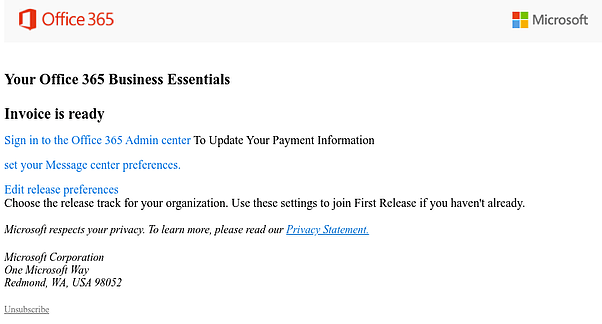
A sample of the phishing email. (Source: PhishLabs) In the event a recipient clicked on the email's embedded link, the campaign redirected them to a fake login page for Office 365. PhishLabs found that those responsible for this campaign specifically targeted admins' credentials. Fraudsters have various motives for going after admins. By compromising an admin account, they can potentially gain control of the other email accounts that are associated with a given domain. They can also leverage an admin account's elevated privileges to create other accounts for the purpose of sending out additional attack waves. That's exactly what happened in this attack. PhishLabs found that the digital fraudsters gained a degree of administrative control over the sender's Office 365 infrastructure. They then abused that control to create a new account and further distribute the campaign. This attack operation highlights the need for organizations to defend themselves against phishing attacks. Towards that end, they should educate all employees--including their administrators--about some of the most common phishing attacks that would seek to compromise their business account credentials. This resource is a good place to start.

