
Digital fraudsters have launched a new phishing campaign whose attack emails instruct recipients to click on a "Keep same password" button. Bleeping Computer observed that the phishing campaign uses attack emails that arrive with "Account Update" as their subject line. The emails list recipients' email addresses and inform them that their account password is set to expire at a strangely exact arbitrary time. They then inform recipients that they can keep their current passwords so long as they click on a "Keep same password" button embedded within them.
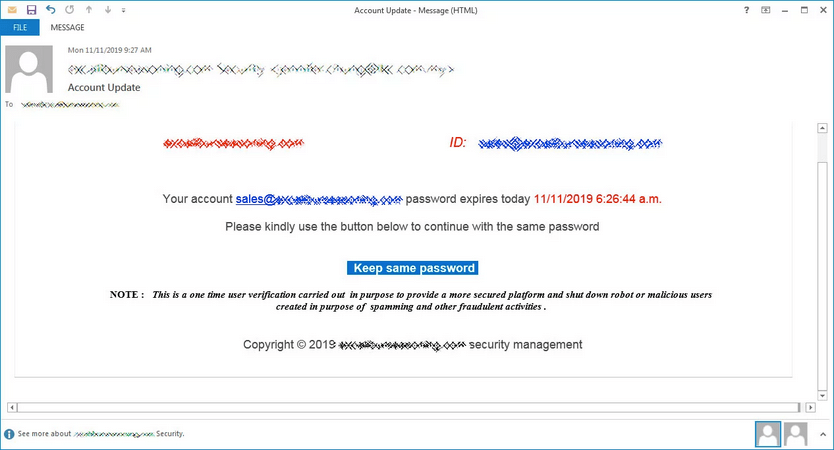
A sample of the phishing email (Source: Bleeping Computer)
Your account [email protected] password expires today 11/11/2019 6:26:44 a.m. Please kindly use the button below to continue with the same password Keep same password NOTE : This is a one time user verification carried out in purpose to provide a more secured platform and shut down robot or malicious users created in purpose of spamming and other fraudulent activities . Copyright © 2019 example.com security management
Not surprisingly, the "Keep same password" does not lead users to an IT portal where they're given the chance of keeping the same password. That's because their password is not set to expire to begin with. Instead, the email redirects users to a fake page that asks them to authenticate themselves with their corporate mail server. Users who comply inadvertently hand over their account credentials to the individuals responsible for the campaign. Those malicious actors can then use those details to perform a business email compromise (BEC) attack, at which point they can then commit CEO fraud and/or stage other secondary attacks. This attack highlights the need for organizations to protect their employees against attacks that attempt to trick recipients into handing over their account credentials. They can do this by leveraging their security awareness training programs to educate their workforce about some of the most common types of phishing attacks. This resource is a great place to start.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

