
In 2022, phishing attacks have not only increased substantially, but they have also taken a new turn of events. According to the Agari and PhishLabs Quarterly Threat Trends & Intelligence report, phishing attacks are gradually being delivered through a wide range of online platforms. The classic email phishing attack technique has increased slightly, while other significant phishing trends include:
- Impersonation scams through social media.
- Dark web threats, such as credit card fraud.
- Business Email Compromise (BEC) attacks.
- Hybrid Vishing attacks.
Some detail about how enterprises and consumers are targeted by phishing attacks on these diverse platforms is worthy of deeper exploration.
Phishing Threat Trends
As compared to Q1 2021 this year's volume of total phishing sites showed a steady growth of 4.4% from January to March. Furthermore, it is anticipated that these numbers would increase throughout 2022. Financial businesses were the top targets, affected mostly by credential theft phishing. While the incidence of this method declined by 7.4% from Q4 2021, it was still a remarkable 53.8% out of all attacks. The entire technology sector was targeted more in Q1, notably social media (21.5%), webmail/online services (5.5%), ecommerce (1.9%), and cloud storage/hosting. The largest increase of attack volume of credential theft (+9.6%) was reported in the social media industry.
Paid domain registrations or compromised sites were primarily used to stage the majority of phishing sites. This staging method is the first instance in five consecutive quarters, representing the highest of 52% of abused paid services from all incidences. The most common staging method was through compromising existing websites 35.1%.
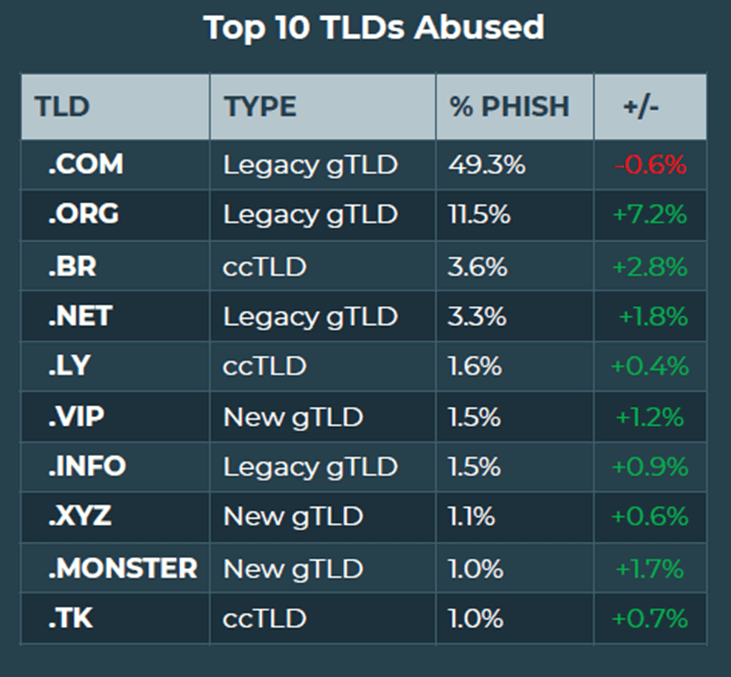
66% of phishing sites were staged on legacy generic Top-Level Domains (gTLDs), which contributed to almost half of all domain abuse phishing activity. Of course, these dizzying numbers are more easily understood in the chart from the report.
Credential theft still reigned supreme in all of the threats in corporate email systems. What is interesting to note is that employees are treating many messages with high caution. However, 82% of the reported emails were identified as “No Threat Detected”. While this heightened sensitivity could generate some cynicism about the value of security awareness training, the report notes that:
“While the majority of employee-reported emails are not classified
as malicious, the identification and reporting of suspicious activity
by a trained workforce is needed to prevent attacks that increasingly
make it past email filters.”
In 2022, it is somewhat unbelievable that 419 “Nigerian Prince” response-based attacks have increased by 3.3%. The fact that this decades-old scam still exists is almost breath-taking. Prior to the internet, these scams were transmitted via fax machines. Unfortunately, the report does not indicate the success rate of these scams, but their continued existence would suggest that they are still effective.
Social Media Threat Trends
The volume of threats from social media channels has advanced 27% from Q4 to Q1 single-handedly. This is a 107% increase targeting enterprises. Impersonation scams are the most frequent method of social media attacks, followed by fraud, and traditional account compromise techniques. Financial institutions still remain the primary target of social media attacks.
Dark Web Threat Trends
The top dark web threat cited in the PhishLabs report is credit card fraud. The dark web is highly famous for publishing stolen card data, which has contributed 53.7% from the total share of dark web threats, despite a 20% decline in Q1. The second most common dark web threat is the sale of corporate credentials. 64% of the stolen data was primarily marketed on carding marketplaces and forums. Forums gained a large 9.3% increase of activity from all dark web marketplaces.
Similar to social media attacks, financial institutions are the most targeted industries for dark web attacks. Credit unions, and Financial Services companies round out the list.
Conclusion
The report indicates technological and strategical improvements in phishing tactics, and enterprises are targeted more than private consumers. Phishing attacks have leveraged various media to execute malicious activity. Apart from the traditional email delivery mechanism, social media is the highest trending platform. Organizations need to be vigilant against these scams and carefully maintain a presence on these platforms to confirm their authenticity and validity to avoid phishing activity, and to secure the name of the company.
One way for organizations to protect against phishing attacks is to enforce email filters, and apply security protocols in their systems to reduce the impact of credential theft attacks. While it is true that some staff members will become overly cautious, security awareness training is still a valid and valuable defence.
Organizations should pay close attention to the diverse platforms that are available today which allow threat actors to easily perform many fraudulent activities. Phishing attacks are being executed in various forms, using myriad tactics. It is the responsibility of each organization to address any phishing related activities for the awareness of consumers and even employees. Proper monitoring of these platforms, and the application of appropriate security protocols and mechanisms to deter phishing threats is a valuable security approach.
About the Author: Dilki Rathnayake is a Cybersecurity student studying for her BSc (Hons) in Cybersecurity and Digital Forensics at Kingston University. She is also skilled in Computer Network Security and Linux System Administration. She has conducted awareness programs and volunteered for communities that advocate best practices for online safety. In the meantime, she enjoys writing blog articles for Bora and exploring more about IT Security.
Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

