
A budding ransomware group donated part of the ransom demands that it had previously extorted from its victims to two charities. On October 13, the Darkside ransomware group announced the donations in a blog post on its dark web portal. As quoted by ZDNet:
As we said in the first press release - we are targeting only large profitable corporations. We think it's fair that some of the money they've paid will go to charity. No matter how bad you think our work is, we are pleased to know that we helped change someone's life.
The ransomware gang specifically made donations of 0.88 BTC (worth approximately $10,000) to two charities: Children International, a global non-profit organization dedicated to helping children in poverty, and The Water Project, an organization which works to provide clean water to villages in sub-Saharan Africa.
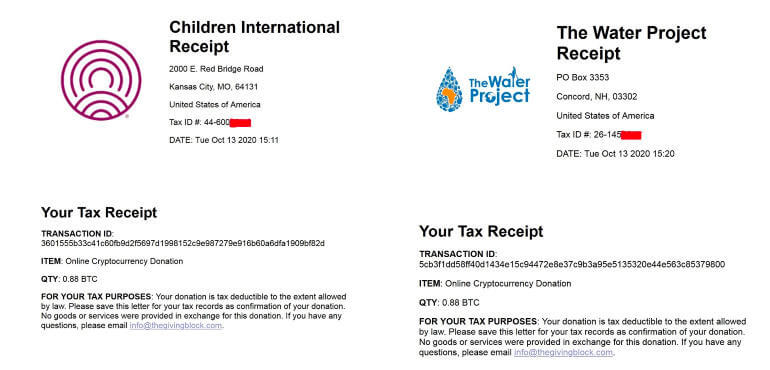
Screenshots of the tax receipts that Darkside received for donating to the two charities. (Source: ZDNet) Reporters at BBC News reached out to both charities about the donations. A spokesperson from Children International clarified that the organization would not keep the gift if it constituted stolen funds, whereas The Water Project had not responded to its requests for comment at the time of reporting. BBC News also contacted The Giving Block, a platform which helps non-profit organizations actively raise cryptocurrency funds. That platform said that it was still investigating the matter and that it would return the funds to their rightful owner if it ultimately learned that they were stolen monies. It's unclear why Darkside, which has been active since August 2020, donated part of its ransom demands to Children International and The Water Project. What is clear is that this charitable act does not negate the harm Darkside caused to its victims. The monies it donated didn't belong to the group in the first place. Given the ongoing campaigns of Darkside and other ransomware gangs, organizations and users alike should take steps to prevent a ransomware infection from occurring in the first place. This resource is a good place to start.

