
Security researchers spotted a new ransomware strain called "Ransomwared" demanding explicit pictures from its victims as a means of payment. Upon successful infection, Ransomwared runs its encryption routine, appending the file extensions ".ransomwared" and ".iwanttits" to each file it encrypts. Given the names of the file extensions, it's not surprising that this particular ransomware family wants something other than bitcoins from its victims. Indeed, it specifically asks that victims send over their "tits."
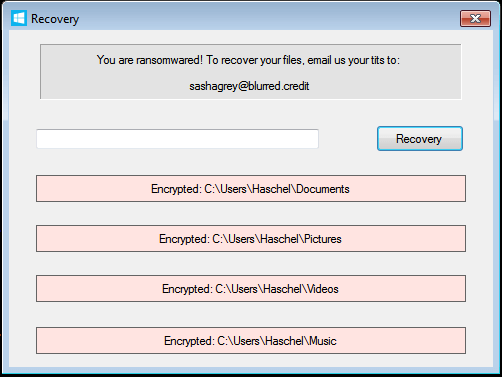
Ransomwared unlock code UI. (Source: Emsisoft) Emsisoft feels that this request might contain its fair share of ambiguity. As it explains in a blog post:
We’re not sure whether the threat actor wants bodily parts or birds – but we suspect the former – and nor are we sure how the actor would know whether said bodily parts/birds actually belong to the victim. So perhaps sending a photo of this handsome chap would suffice.

Chestnut-bellied tit. Image credit to Robert tdc. That being said, there's good news for victims of this threat. Emsisoft succeeded in developing a decryption tool for this particular ransomware strain. Victims can thus recover their files for free without having to make any sort of ransom payment. Victims of Ransomwared can access the decryptor here. If they have any trouble using it, they can reach out to Bleeping Computer for support here. Emsisoft's research did not provide an explanation of the distribution channels employed by this new ransomware strain. It also didn't elaborate on the method used by the security researchers to develop the decryption tool. With that said, users and organizations should realize they're still vulnerable to a host of other ransomware families that might not suffer from any discernible flaws. They should therefore take it upon themselves to protect themselves against a crypto-malware infection. One of the best ways they can do this is by using these tips to prevent an infection in the first place.

