
Data breaches remain a constant concern among boards and executives. Part of the reasoning behind this anxiety is the cost of responding to a data breach. Most years, not only does the per capita cost of a record compromised in a breach go up – so, too, does the total organizational cost. For 12 years, Ponemon Institute and IBM Security have been tracking the financial burden of a data breach. They found that per capita and organizational costs of a data breach reached all-time highs in their newest research. Additionally, they identified multiple factors, four of which are new, that influence the cost of a security incident. These are just some of the trends discussed by Ponemon and IBM in their 2017 Cost of a Data Breach Study. Let's now dive into the report's major findings.
How Ponemon and IBM Calculate Data Breach Costs
Ponemon Institute and IBM Security compute the cost of a data breach using activity-based costing (ABC). For this method of calculation, they first identify activities for detection and response, such as launching investigations, organizing incident response teams and conducting public outreach. They then assign a cost to an organization's actual use of these activities, which the company submits to Ponemon and IBM as part of their participation in their research. Once a company provides all its estimated costs for its activities associated with a data breach, Ponemon and IBM categorize the costs as direct, indirect and opportunity. Direct costs refer to how much companies spend on addressing the consequences of a data breach and helping victims, expenses which include hiring forensic experts and offering identity theft protection services to victims. Indirect costs are time, effort and other internal resources that organizations dedicate to responding to a data breach, with costs ranging from reputation loss to time spent on notifying victims. Opportunity costs are the lost business opportunities that result from a decrease in reputation capital after the public and the media have learned about a breach. Each annual Cost of a Data Breach Study also looks at activities that fall into one of four cost cores: detection or discovery, escalation, notification and post data breach.
Key Data Breach Cost Findings
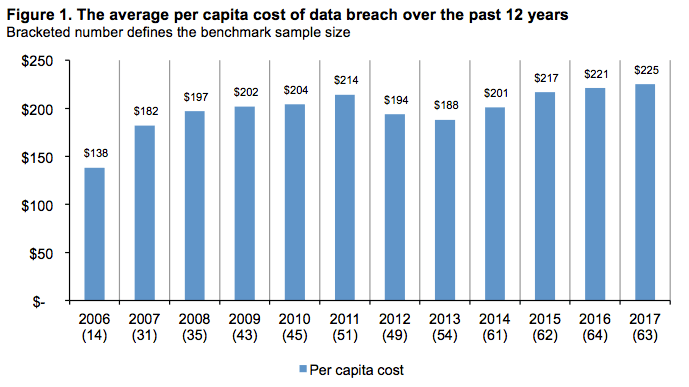
For its 2017 report, Ponemon and IBM interviewed 1,900 individuals from 419 organizations in 11 countries and two regions (including 63 US companies operating from 16 industry sectors) that suffered at least one breach in the previous 10 months. They asked respondents how many records the incident affected and what percent of their organization's customer base it breached. They also asked about their company's discovery and recovery efforts. The average cost of a lost or stolen record compromised in a data breach (i.e. the per capita cost) increased from $221 in their 2016 study to $225. This cost consists of $146 spent on indirect costs and $79 on direct costs. By comparison, organizations that suffered a data breach the year prior spent $145 and $76 on indirect costs and direct costs, respectively.
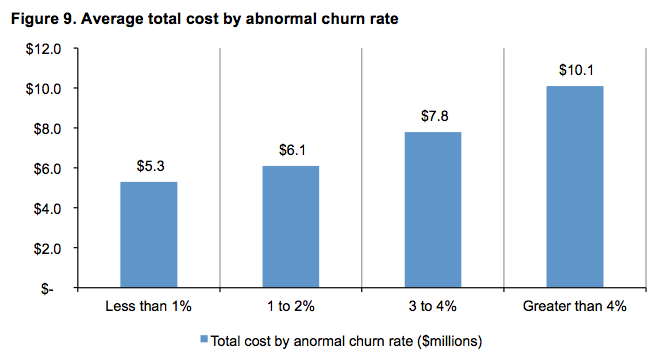
2017 Cost of a Data Breach Study, page 7 The total average organization cost of a data breach also went up. In its 2016 study, companies spent an average of $7.01 million. They spent $7.35 million a year later, thereby replacing the previous all-time high of $7.24 million back in 2011. Aside from these changes in cost, Ponemon and IBM detected some other notable developments. For instance, abnormal churn, or the greater-than-expected loss of customers over the normal course of business, increased by five percent over a year's time. This development is important because abnormal churn is oftentimes associated with higher data breach costs. Those organizations that experienced less than one percent abnormal churn in the 2017 study spent an average of $5.3 million in response to a data breach. By comparison, those with an abnormal churn rate greater than four percent spent $10.1 million on average.
2017 Cost of a Data Breach Study, page 12 Their report also found that the average size of a data breach decreased by 1.9 percent. The number of breached records for the latest report ranged in total from 5,563 to 99,500, with an average of 28, 512 breached records. Ponemon and IBM intentionally excluded incidents that exposed more than 100,000 records, as they felt this level of impact was not indicative of what most organizations experience in a breach. The 2017 study reveals that size matters when it comes to calculating data breach costs. On average, organizations that experienced a breach of less than 10,000 records paid an average of $4.5 million. This is less than half of the $10.3 million paid by companies that suffered a breach of more than 50,000 records.
Understanding the Causes and New Cost Factors of a Breach
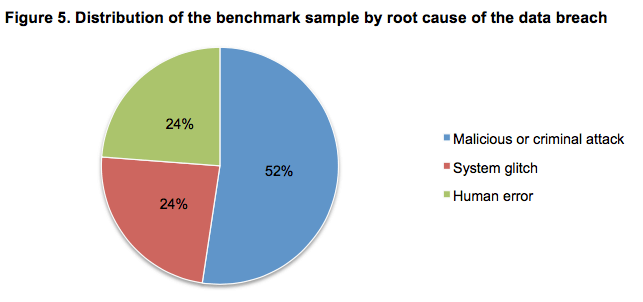
When it comes to causing a breach, malicious attacks were the commonest and costliest source. Malicious and criminal attacks played a part in 52 percent of breaches reported to Ponemon and IBM, dwarfing negligence (24 percent) and system glitches (24 percent) as causes. Those attacks generated an average per capita cost of $224, which is greater than both those costs attributed to system glitches ($209) and human error ($200).
2017 Cost of a Data Breach Study, page 10 Irrespective of cause, several factors traditionally influence the per capita and organizational costs of a data breach. In addition to abnormal churn and size, the time it takes to identify and contain a breach also affects cost. In their 2016 report, Ponemon and IBM discovered it took organizations an average of 201 days to identify a breach and 70 days to contain. These figures dropped down to 191 days and 66 days, respectively, in their latest study. This latest report also identified four new factors that oftentimes influence the cost of a data breach. For instance, using security analytics and appointing a Chief Privacy Officer (CPO) reduced the per capita cost of a data breach by $7.70 and $4.30, respectively. By contrast, extensive use of mobile platforms increased the per capita cost of a security incident by $6.50, whereas compliance failures cost organizations an additional $19.30 in per capita costs.
Detection, Escalation, Notification, and Post Data Breach Costs
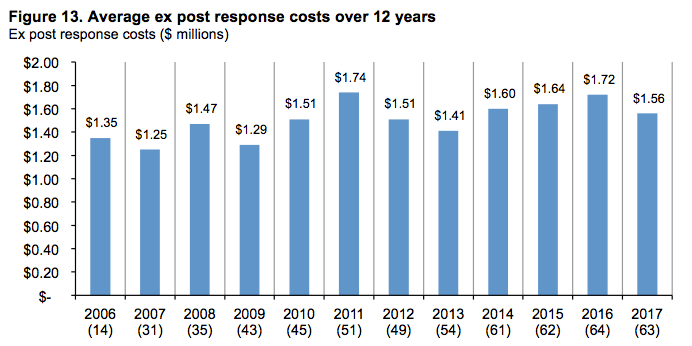
Most of the four data breach cost cores used by Ponemon and IBM increased in their 2017 report. Average costs for detection and escalation, which include expenses for forensic teams, audit services and crisis team management, increased from $0.73 million in their 2016 report to $1.07 million in their latest study. Similarly, the notification costs associated with contacting victims following a breach rose from $0.59 million to $0.69 million in that same time period. Post data breach costs, or expenses following a breach like legal expenditures, product discounts and identity theft protection services, decreased between their 2016 and 2017 report from $1.72 million to $1.56 million.
2017 Cost of a Data Breach Study, page 15 That being said, organizations can assuage these costs by investing in security and deploying new technology. Investments in governance, risk management and compliance (GRC) can help drive down detection and escalation costs, for example, whereas digital insurance can reduce post breach expenses. Many organizations recognize they can reduce the risks and consequences of a data breach with strategic investments in key technologies and security controls. Some of the most profitable investments Ponemon and IBM tracked in their 2017 report were incident response plans, use of encryption, participation in threat intelligence sharing, employee training and data loss prevention technologies. Training and awareness programs registered among 60 percent of participating organizations, followed by encryption (55 percent) and endpoint security solutions (49 percent). At the same, both endpoint security solutions and security intelligence solutions saw a 13 percent increase since 2010 among companies.
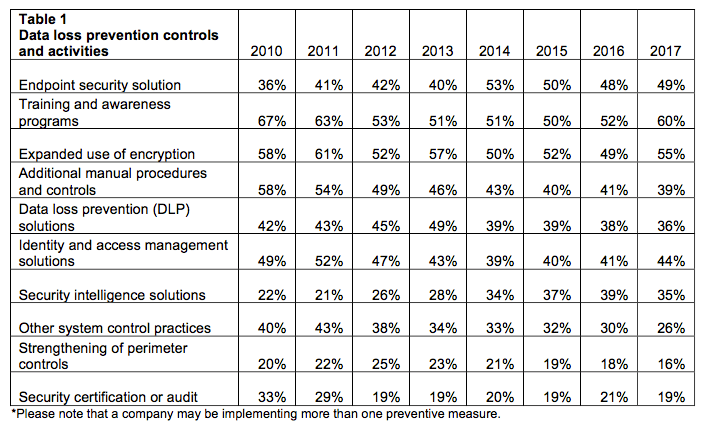
2017 Cost of a Data Breach Study, page 19
A Call to Action
While it's promising to see organizations making investments in their security posture, the fact that at least 40 percent of organizations interviewed by Ponemon and IBM don't use security controls like training and awareness programs, encryption, and endpoint security solutions is alarming. Fortunately, it's never too late to embrace these measures. Executives can learn about the importance of the CIS Critical Security Controls by clicking here. For more findings from the Cost of Data Breach 2017 Study, download the full report here.

