
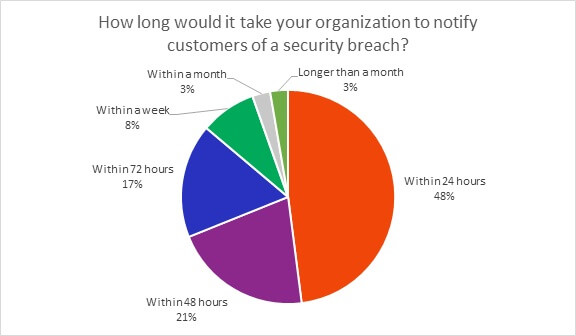
Defining a data breach can be tough for a lot of organizations. However, since the introduction of the General Data Protection Regulation (GDPR) in 2018, organizations that operate in the EU need to follow regulatory guidelines that can have real business implications if ignored. But when a cyber incident hits your organization, do you know if it needs to be disclosed to the public? How prepared are you to let your customers and authorities know? Do you have a tried and tested incident response plan in place? To help us learn more about this, during Infosecurity Europe 2019 in London, we asked 298 IT security professionals a few significant questions around the subject. Here is what we found out. One of the standout headlines from when the GDPR was implemented, was the need for organizations to declare a data breach within 72 hours. Based on our survey, a majority said they were able to comply, but 14 percent of organizations are still not compliant.
According to the GDPR, a data breach is a type of security incident but that not all security incidents qualify as a data breach. There are three controlling principles at play here, and any single one or combination constitutes a breach.
- Confidentiality Breach – an unauthorized or accidental disclosure of, or access to, personal data.
- Availability Breach – accidental or unauthorized loss of access to, or destruction of, personal data.
- Integrity Breach – an unauthorized or accidental alteration of personal data.
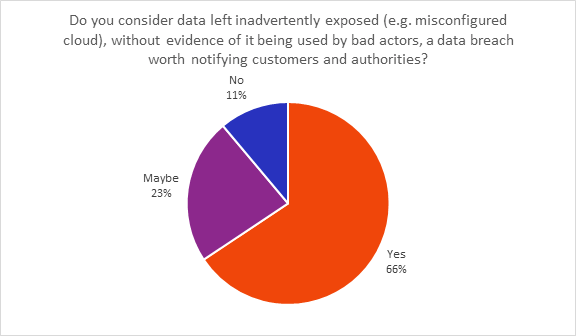
Keeping this in mind, responses from the survey showed that IT professionals still have some uncertainty around whether certain types of cyber incidents require disclosure. Some incidents may not actually involve an attack (e.g. cloud misconfiguration), and attacks aren’t necessarily aimed at stealing data (e.g. ransomware). Public exposure of cloud data is often due to accidental cloud misconfiguration, not a malicious attack. In the case of publicly exposed data through misconfigured cloud storage, 34 percent said they would not disclose, or weren’t sure they’d disclose if there was no evidence of bad actors getting their hands on the data.
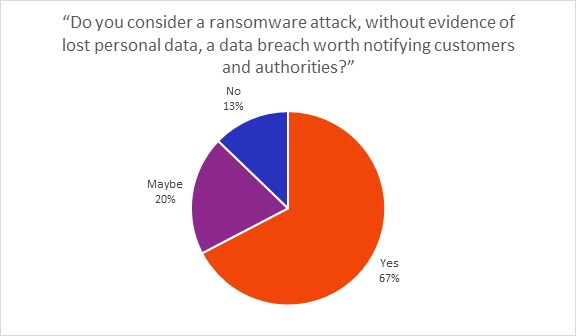
The results were similar with ransomware as 33 percent of respondents were also unsure of whether attacks would constitute an obliged breach triggering notification. However, as 67 percent allude to, GDPR, tells us the specific incident details matter – the moment personal data is accessed, a few different principles come into play. While the loss of access to data might only be temporary and not allow us to apply the availability principle (presuming you can restore from a backup plan), the “unauthorized access” part of the confidentiality principle could be invoked once again depending on the particular details.
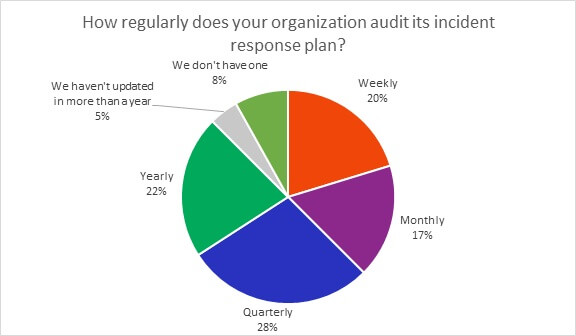
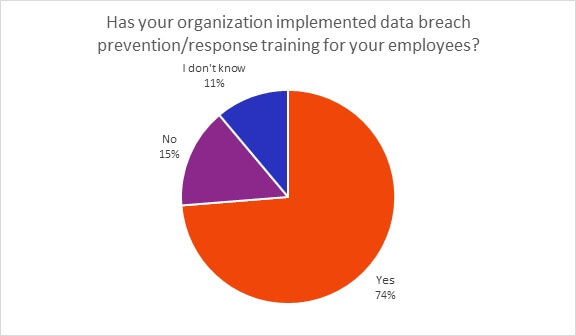
The famous slogan, “it’s not a question of if you will be breached, but when” is often spoken about in the IT security world. That’s why now more than ever it’s vital to the business to have a concrete incident response plan in place, not just a strategy. Not only that, organizations also need to be of the mindset that employees are actually the strongest link in the business, not the weakest. Having a plan in place to respond to a data breach is essential, and having a team in place that can implement the plan is equally as vital. In the most part, this set of questions allows us to be optimistic. Most organizations indicated that they were taking measures to prepare for a data breach with incident response plans and employee training being an important part of that. Eight-seven percent update their incident response plans annually or more often. Only 5 percent have waited longer. Also, it was good news to see 74 percent of respondents having implemented data breach prevention/response training for their employees, with just 15 percent saying they have done nothing.
Overall, Tim Erlin, vice president of product management and strategy at Tripwire said: “These results are fairly encouraging and indicate that knowledge about GDPR’s requirements around data breaches is spreading. There is still room for improvement, however. Anyone in an information security role should be familiar with the basic requirements of GDPR and what their responsibilities are. The biggest opportunities for improvement are around what constitutes a breach and how to respond to an incident.”
To learn more about how Tripwire can help keep your organization secure, click here.

