
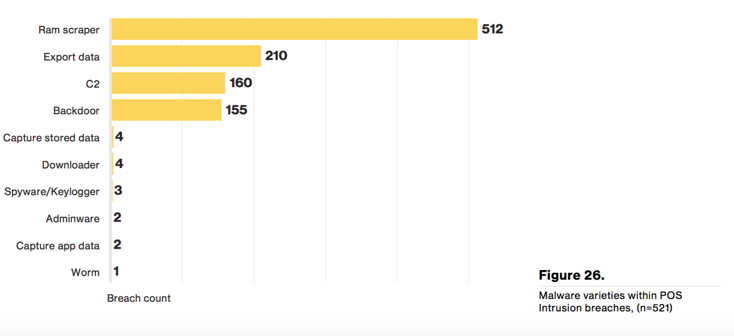
The retail industry’s critical infrastructure, point-of-sale (POS), continues to be plagued with breaches, according the recent Verizon’s 2016 Data Breach Investigations Report. Though retail as an industry depends on POS, the accommodations/hospitality sector this year took the top spot for confirmed POS-related data breaches at 95 percent. (Only 64 percent of breaches in the retail sector were POS-related.) Both retail and accommodations industries were also among the top five sectors that experienced security incidents with confirmed data loss. Though not tracked in the report, payment data seems to be the obvious target for those five industries, with headlines on Hilton Hotels and Trump Hotels supporting that view. Payment card data is a well sought-after item for hackers. Unfortunately, attackers are actively gaining ground on obtaining it. There has been so much momentum that supply and demand has pushed the price of a payment record down to $6 from its value of $25 back in 2011. Even more disturbing is the notion that weak, stolen, or default passwords caused 63 percent of the POS intrusions – this is like leaving your door open for anyone to enter. In response, PCI 3.2 is requesting multi-factor authentication for Card Data Environments (CDE) that include POS devices. This requirement could mitigate hackers' efforts here. The most common behaviors among POS malware include RAM scraping, exporting data (FTP), command centers, and backdoors. One of the most problematic RAM-scraping malware is MalumPOS. What sets it apart from the others is its ability to adapt and reconfigure, allowing it to be easily customized for particular targets. As noted by Trend Micro, this is concerning for popular POS systems, such as Radiant or NCR Counterpoint.
Source: Verizon DBIR 2016, p. 33 To counter threatsm such as MalumPOS, Verizon's report offered some recommendations:
- Improve your authentication to at least two-factor.
- Segment your POS environment.
- Seek monitoring options for POS environment.
There is something else you can do to protect your POS environment. Tripwire Enterprise has distinct POS rules to identify and protect against malicious POS behaviors. 451 Research has published an industry report on this capability.
Beyond The POS
It would be fair to say that all retailers have a web presence. The top confirmed data breach type was web application attacks. The report pointed to the obvious reason of financial gain, with 95 percent of web application breaches being financially motivated. E-commerce servers’ attacks use web shells to access the payment application code, which is then modified with a new feature that will capture the user's input (such as payment card number and CVV). Ongoing trends in e-commerce, as well as this breach report, should be alarming to retailers and consumers. Here are some recommendations we can derive from Verizon's report:
- Assume key logging malware for single factor authentication.
- Validate inputs and uploads.
- Establish patch processes for content and third-party plug-ins.
Some recommendations from the report are helpful, but they do not shed light on how they might affect the quality of customers' experience on affected website. For example, asking a consumer to do multi-factor authentication to purchase an item will be an adjustment for them, and it could limit impulsive and spontaneous online purchasing. The report tracks interesting data points, such as security incidents and breaches by industry.
"Incident: A security event that compromises the integrity, confidentiality or availability of an information asset. Breach: An incident that results in the confirmed disclosure (not just potential exposure) of data to an unauthorized party."
With retail and accommodations, the number of incidents is relatively low (Accommodations: 362 incidents and Retail: 159 incidents) compared to other industries (Finance: over 1300 incidents). This may suggest that they do not have the advanced capabilities to identify and report on potential threats. The ratio of incidents to breaches is also telling, noting a large percent of the incidents to be actual threats (Accommodations: 282 incidents and Retail: 137 incidents).
Indicators of Improvement, Maybe
Most recently, Tripwire conducted a 2016 survey with over 200 Retail IT professionals and compared it with a previous survey in 2014. The results did indicate some improvement in their efforts to combat cyber security. Tripwire’s 2016 survey found that ninety percent of the respondents believe they could detect a data breach on critical systems in one week or less. In 2014, seventy percent of respondents believed they could detect a breach in one week or less. Yet according to a report by Arbor Networks, it takes retailers an average of 197 days to detect advanced threats on their networks. This increase in confidence regarding detection is good, but it does not seem to reflect reality. In both 2014 and 2016, fifty-nine percent of the respondents said their breach detection products were only partially or marginally implemented. The retail industry is taking steps to improve its cyber security, but based on this Verizon report, it has not been enough. With security spending per employee for retail being $169 while other industries are spending $326 to $684 per employee (Gartner 2014), it’s time for bolder improvements. Consider the consequences. The total average cost of a data breach worldwide has increased 15% from 2014 to 2015 to more than $3.5 million (Ponemon Research). The Verizon report has offered great insight into the problems. Let’s move to better protection with this greater understanding. Title image courtesy of ShutterStock

