
Scammers are impersonating governmental departments within the State of Texas to send out fake Requests For Quotations (RFQs). On September 21, Abnormal Security revealed that it had spotted an attack email that impersonated the Texas Department of State Health Services. Scammers used spoofing techniques to camouflage the sender address as an account that was affiliated with the official dshs.texas.gov domain. Even so, the Reply-To address referred to an email account affiliated with finance-nycgov.us, a domain which someone first registered in early July 2020 presumably for the purpose of spoofing nyc.gov. In the attack email, the scammers informed the recipient organization's sales department that they were interested in purchasing 20 laptops and 200 external hard drives on behalf of the Texas Department of State Health Services. The attackers provided a billing address and a phone number for the items cited in their email. This helped to give their efforts a sense of legitimacy. As quoted by Abnormal Security in its research:
There is no ship to address (listed as TBD), and the phone number provided is not associated with the bill to address, although the area code is in Texas and does match the area code for the department of state health services phone number. This is a social engineering tactic aimed to engage recipients into requesting the ship to address, either by email or phone.
Ultimately, the scammers used those techniques to trick the recipient into opening a PDF document disguised as a RFQ.
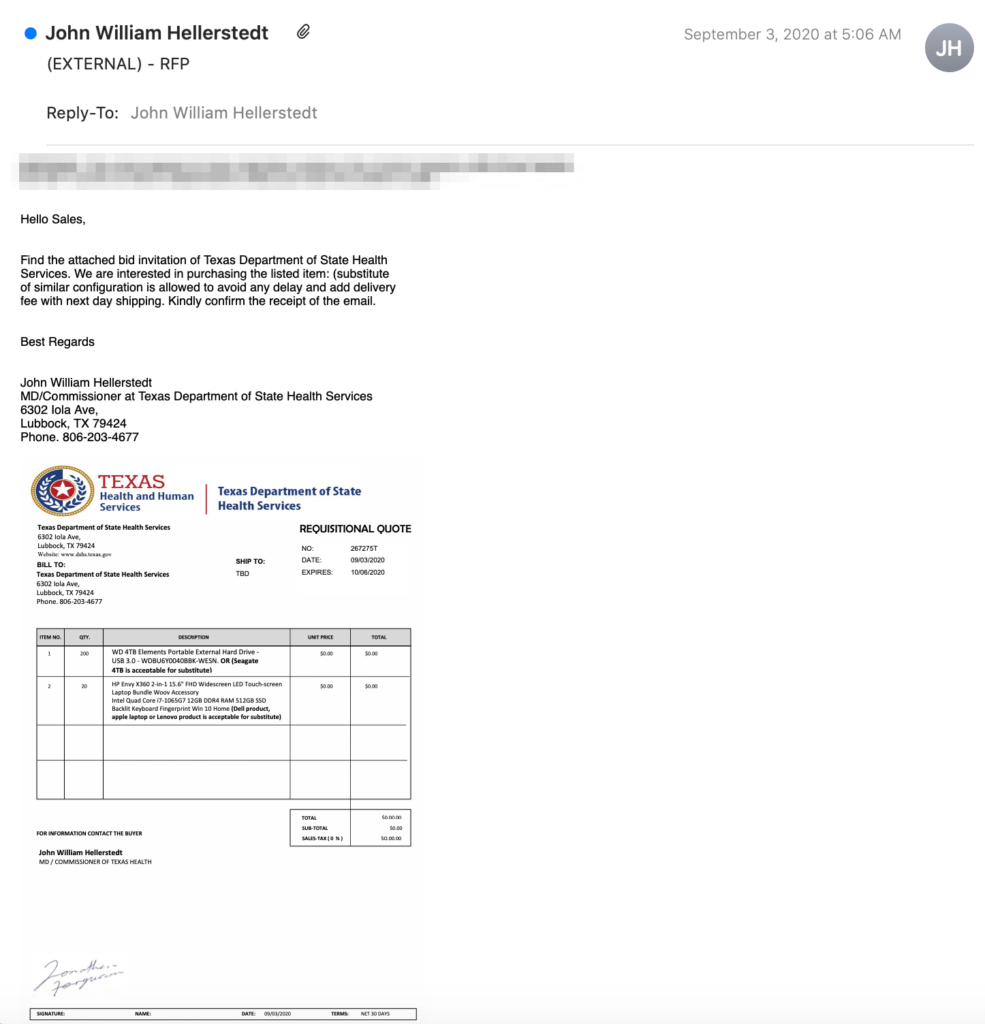
Screenshot of the attack email. (Source: Abnormal Security) In the event the recipient complied and or responded to the email, the scammers could then use that line of communication to trick the sales department into approving the order and sending over the goods. The targeted organization would ultimately not receive payment for the goods, however. It would thereby incur a loss upwards of tens of thousands of dollars. At the time of publication, the attack emails associated with this campaign had ended up in as many as 50,000 mailboxes. The attack campaign described above highlights the need for organizations to defend themselves against phishing attacks. They can do so by educating their employees about some of the most common types of phishing campaigns that are in circulation today.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

