
Why is cybersecurity important to Education?
Acknowledging recent reports of ransomware targeting educational institutions, it is no wonder that there have also been articles that attempt to lure in readers with “free” tools. What is disappointing is that these “free” tools are little more than marketing pieces that direct you to click on readily available documentation from Microsoft or Google. Additionally, the frameworks on which these guides are based are freely available via the National Institute of Science and Technology (NIST). It’s important to note that the educational community is a target for cybercriminals and not just from a ransomware angle. Primary educational institutions still face off against students attempting to manipulate grades or just create random chaos on systems with the purpose of causing a delay or canceling school. The research conducted by secondary institutions is also a target, especially by nation-state actors. All institutions should take steps to secure their environments. The best way to do this is to follow the proven guidance of the Center for Internet Security’s Critical Controls, particularly with regards to the six Basic Controls. Most K-12 school departments will already have #1 and #2 covered, but #3 through #6 might be a challenge depending on available resources and budget allocations. Let’s have a look at how educational institutions can implement all six of these basic security measures.
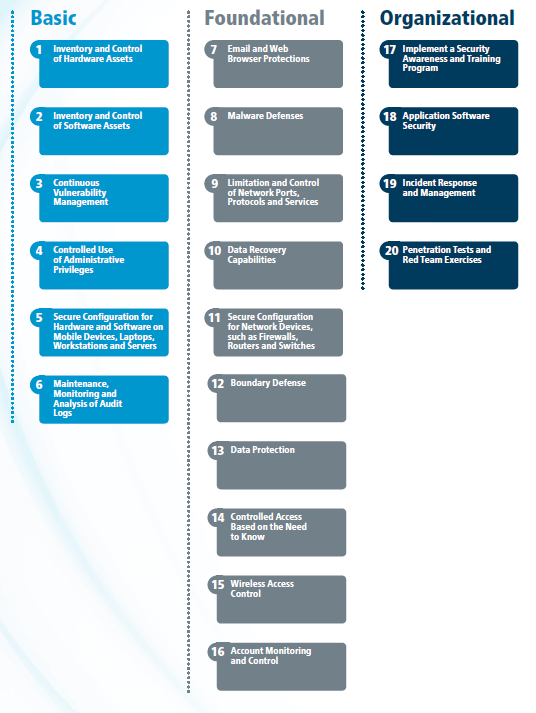
Figure 1 CIS Controls™ v7.1 To get the most out of the CIS Controls™, it is important to understand your organization’s classification. Most K-12 schools tend to have a small staff, often sharing a single person between multiple schools. CIS® would classify this type of organization as Implementation Group 1 (IG1), "small to medium-sized with limited IT and cybersecurity expertise to dedicate toward protecting IT assets and personnel." The main focus is to keep the business operational while protecting financial and employee data. A few schools may be classified as IG2, "employs individuals responsible for managing and protecting IT infrastructure. These organizations support multiple departments with differing risk profiles based on job function and mission." Larger organizations would be classified as IG3, "employs security experts that specialize in the different facets of cybersecurity (e.g., risk management, penetration testing, and application security). IG3 systems and data contain sensitive information or functions that are subject to regulatory and compliance oversight."
CIS Controls™ - Basic (1-6)
CIS Control 1 – Inventory and Control of Hardware Assets
Is it any wonder that the number one control is knowing what you have? Without an accurate understanding of what is connected to your network, how can you protect it all? The inventory could be as simple as a spreadsheet or part of an entry-level ticketing system. Equally important is identifying unauthorized assets. This might be tricky, but reviewing DHCP logs and physical inspection are likely the practices in place. Simple tools such as network IP scanners may also provide information about the devices found, assisting staff in identifying rogue devices.
CIS Control 2 – Inventory and Control of Software Assets
A bigger challenge is understanding what software is installed on your systems. Who has access to install software, and is it necessary, required, and approved for installation? This control requires the organization to have an up-to-date list of all authorized software installed on any business system. The software must also be supported by the vendor, which includes the operating system. Unauthorized software must be identified and approved, if necessary. Otherwise, it should be removed. Several commercially available endpoint protection vendors offer a whitelisting capability, so this ability may already be "in-house."
CIS Control 3 – Continuous Vulnerability Management
"Organizations that do not scan for vulnerabilities and proactively address discovered flaws face a significant likelihood of having their computer systems compromised." That statement should scare you, and this is the first control where the recommendation for IG1 is very minimal. CIS recommends that small organizations focus on protecting systems by deploying automated OS and Software Patch Management tools. Luckily, Microsoft provides Windows Server Update Services (WSUS) at no cost, and Apple has Profile Manager. Both of these tools can be installed and configured quickly and easily. Additionally, WSUS can be extended to support third-party software, updating via API calls using Local Update Publisher.
CIS Control 4 – Controlled Use of Administrative Privileges
Default passwords for devices and systems are widely known and easily discovered on the Internet. Your first step when deploying anything should be to change them as soon as the device is unboxed. Initiate Least Privileged Access on all user accounts to counteract malicious email attachments, downloads, and "drive-by" malware. This can be accomplished by creating dedicated administrative accounts for users that require higher privileges. Attackers can also attempt to “elevate privileges” by guessing or cracking your passwords. The more administrative accounts you have, the higher the chances of this occurring.
CIS Control 5 – Secure Configuration for Hardware and Software
As with CIS Control #3, the recommended implementation of Control #5 is simply to protect your assets. Doing so requires that you document secure configuration standards for all of the authorized OSes and applications identified in Control #2. There are plenty of excellent sources for this configuration information, including CIS and NIST. Each website provides coverage for all current operating systems and numerous applications. With the guidelines in hand, you now have to find tools to implement the recommendations. For Microsoft environments, creating a Group Policy in Active Directory will typically suffice.
CIS Control 6 – Maintenance, Monitoring, and Analysis of Audit Logs
As part of Control #5, you will likely be configuring your systems to meet the requirements for Control #6. Almost all security configuration guidelines and compliance regulations require that auditing of the operating system or network device be enabled. Doing so assists you in determining when a change occurred and by whom. Logging records are often the only evidence of a successful attack. For IG1 organizations, the recommendation is to enable this locally on the system. Reviewing these logs on a periodic basis and evaluating them against your inventory from Control #1 will help you to confirm that all systems are configured for logging.
Resource Pooling to Improve Security
It’s important to note that the controls discussed above are hierarchical, with the Basic Controls setting the foundation for the levels that follow. With that said, the key to success with regards to implementing #3 through #6 is to not look for “free” solutions. While the information is "free," the investment to implement them is time, a very valuable commodity for K-12 institutions that may only have one or two folks on staff for addressing IT needs. The goal must be to find solutions that can assess systems and networks, provide clear and concise actionable data, and automate some, if not all, of the remediation steps. To that end, there are plenty of open source and commercial applications available that can assist. The key is to find the ones that provide the breadth of coverage for the environment, offer integrations within the security stack, and integrate with other tools to help confirm controls #1, #2, and #4. The potential to fund cybersecurity deficits may also exist on a county, regional, or even state level. Municipal Boards of Education should explore potential partnerships to help achieve these controls and progress to moving onto the Foundational Controls that CIS provides. This pooling of resources can help to reduce overall costs.
Mastering Security Configuration Management
Master Security Configuration Management with Tripwire's guide on best practices. This resource explores SCM's role in modern cybersecurity, reducing the attack surface, and achieving compliance with regulations. Gain practical insights for using SCM effectively in various environments.

