
Detecting and preventing malicious software from executing on critical systems has received a lot of attention in the information security industry lately. Being able to detect new applications, drivers and files is what Tripwire Enterprise excels at. However, there are quite a few options for a motivated attacker to take advantage of built in applications and tools within the operating system to compromise, pivot and pilfer critical company data. The attacker is only using tools provided by the target organization, essentially “living off the LAN.” On many popular distributions of Linux, a utility called Netcat is installed. Netcat is a powerful tool for system administrators and is commonly installed on many servers, including some Windows systems. It allows the user to connect and communicate to a remote port, or create a listener to allow remote connections in. By having control over the outbound TCP or UDP connections, Netcat can be used as a port scanner to both identify open ports but also to fingerprint the services and applications available. A simple command of ‘nc –nv –w1 <ip> <port range>’ will scan the target IP address for the ports designated.
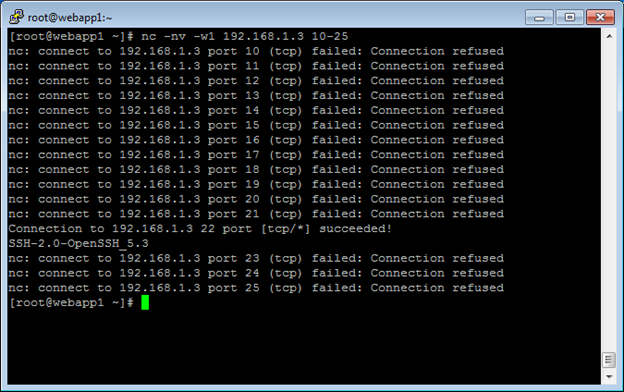
Figure 1: Netcat Portscan As seen in Figure 1, the netcat client quickly and quietly scanned 192.168.1.3 on ports 10 through 25, identifying that port 22 is listening using SSH-2.0-OpenSSH 5.3. By interacting with specific ports, we can gain even more valuable information from the system, including the application name, version and supporting operating system.
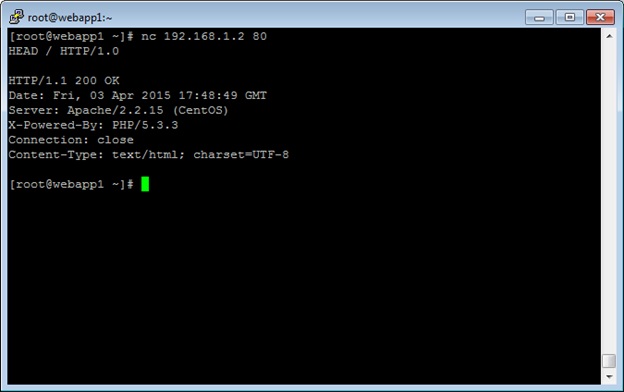
Figure 2: Netcat Fingerprinting Figure 2 shows that by interacting with the HTTP service on the target machine, we can infer that the machine is running Apache version 2.2.15, PHP 5.3.3, and is running on a CentOS operating system. While information leakage like this may not be necessarily dangerous, there are more nefarious actions that Netcat allows the attacker to perform, including opening backdoors and transferring files between systems. Netcat has an option to execute a program and pass input from the listener to the program. When executing /bin/sh on Linux machines, or cmd.exe on Windows machines, you open a backdoor into the target system. Fortunately for security administrators, the -e option may not be included in the version of Netcat installed. To work around this, the attacker would then simply setup a relay by creating a Netcat listener which reads from standard input from a FIFO file. Then the attacker could then pipe the command to a Netcat command which connects to the localhost on port 22, again redirecting standard output into the FIFO file referenced earlier. To act as a relay, simple connect to a different IP address instead of localhost. While there are methods of transferring files, such as SCP, FTP or TFTP, these are generally either monitored closely or blocked via the firewall. The Netcat tool allows the contents of a file to be piped into or out of the command, allowing the attacker to pilfer data out of the network or upload malicious files to the system. Fortunately, Tripwire can help detect the usage of Netcat in your environment. Tripwire Log Center’s built in correlation rules quickly detect and alert on port scans, including the port scan described earlier. Additionally, Tripwire Enterprise Cybercrime Controls detect multiple points along the attack chain. First, any new software installed, including a built-in utility like Netcat, will be detected. Next, any new ports inbound or outbound will be detected. Finally, rules can be created to detect if Netcat is installed on any server on the network. If Netcat is found, the system administrators can make decisions to remove the utility if it is not necessary in order to reduce the attack surface of the server. Controlling a Windows environment can be done with the Windows version of Netcat, but may not be as prevalent in the Windows environment since it is not a built-in tool. Alternatively, Microsoft has provided attackers tools based on SMB, such as Windows Management Instrumentation Command-Line (WMIC). To execute remote commands, you will need an administrator level account. Unfortunately, with pass-the-hash being so prevalent within Microsoft, it may not be too difficult to obtain an administrator level account. Besides WMIC, other built-in tools, such as reg.exe and sc.exe, allow an attacker to control remote machines, with the caveat that they require a compromised administrator account. Since many system administrators use tools like WMIC, reg.exe, and sc.exe, detecting their malicious usage can be quite difficult without reporting false positives. Instead, Tripwire Enterprise users can rely on Change Audit and Critical Change Audit rules to detect any modifications to key files and/or registry settings within their critical infrastructure. Additionally, the Cybercrime Content rules monitor the status of all services on Windows machines. Any interaction with the sc.exe command will trigger these rules and alert the system administrators to malicious activity. While an attacker is much more efficient when using external tools and malicious software, these few examples show that an attack surface is still available to attackers. Fortunately, when understanding the attack chain, there are products that can help detect the chain no matter what tools the attacker has at their disposal.
Mastering Security Configuration Management
Master Security Configuration Management with Tripwire's guide on best practices. This resource explores SCM's role in modern cybersecurity, reducing the attack surface, and achieving compliance with regulations. Gain practical insights for using SCM effectively in various environments.

