
You know what I don’t want to talk about any more? Responsible disclosure. The problem is that, as old as that discussion is for information security, it and the adjacent topics, remain relevant for many other industries.
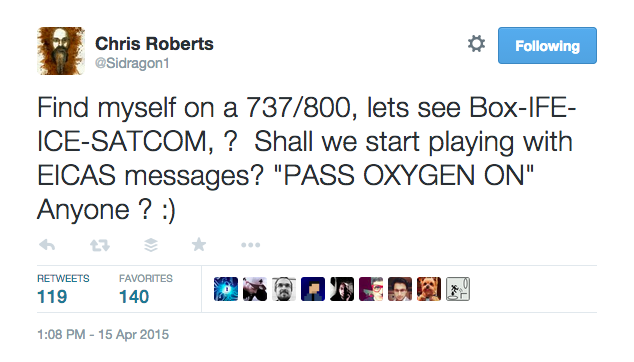
There’s a good chance you caught the media coverage of a recent incident involving Chris Roberts, a security researcher, being removed from a flight for a joking tweet about possible vulnerabilities. Update: FBI claim researcher hijacked a plane during flight Regardless of your feelings about this specific incident, it’s illustrative of a core challenge in the disclosure debate: at what point does publication of research actually increase risk? But, that’s an old debate, which I won’t rehash here. An event you might not have noticed, however, was the publication earlier this month of a Government Accountability Office report titled “FAA Needs a More Comprehensive Approach to Address Cyber security As Agency Transitions to NextGen.” Combine this incident, the GAO report, and some of the recent security research into the vulnerabilities of aircraft systems and you have a startling picture of the changing threat landscape for aviation. I’ll summarize: As we bring more modern IT into an industry where technology has traditionally been closed and expertise contained to a small group of people, a previously centralized and controlled culture is being forced to deal with the basic, but prevalent, security issues more open systems have been confronting for years. To put this another way, hard-core engineering industry professionals often believe that if information about how systems might be exploited is published, then the risk of these systems being exploited will increase. In contrast, most security researchers believe that responsibly disclosing security issues creates positive pressure on vendors to address these issues more effectively. Aviation isn’t the only industry in this position. Energy, utilities, automotive, any industry where operational technology is being integrated or replaced with more IT components experiences this conflict. These are generalizations, of course, and there are extremes on either side, but there’s a core, cultural difference in a response of ‘no one can access this component’ and ‘what happens when someone does?’ Industries that have a life-and-death impact are, understandably, particularly sensitive to this issue. Anywhere failure can actually kill people deserves some special consideration. In aviation, flight safety trumps information security, as it should, but as more and more attacks affect well known organizations, information security is gaining in visibility. There’s a growing recognition that cyber-attacks can have real-world consequences. Despite this change in visibility, security researchers are concerned that if they demonstrate theoretical attacks on aircraft and aircraft systems, which include things like accessing some flight control systems via the in-flight entertainment system, rather than acknowledging the vulnerability and developing a plan to fix it, regulators and airlines will instead respond negatively and aggressively, with the intent to suppress the information. This is a big problem because rather than acting on potential security threats to actively reduce risk, suppression ultimately drives criminal interest and increases risk. While this behaviour is often grounded in a desire to keep dangerous information out of criminal hands, other industries have come to realize that supressing security research just results in less effective response and patching leaving systems more vulnerable to attack. An actively negative response generates more risk, not less.
Are the Threats Targeting Aviation Real?

The aviation industry relies heavily on technology, some of which is directly relevant to the safety of aircraft inflight and others directly impact the service, reputation and financial health of the industry. Despite the critical role technology plays in the safety of air travel, the aviation industry is still not equipped to handle many common cyber-attacks. Some of the challenge is technical, but much of it is cultural, as noted above. While it might seem like the most obvious information security challenge to the aviation industry would be the increasing sophistication of attacks, the reality is that a lack of basic cyber security ‘best practices’ is an obvious next step in improving resilience and limiting risk. As more corporate IT systems and components make their way into traditionally closed aviation technology systems, they bring with them a number of security issues. These issues aren’t new to traditional IT, but they present new challenges when they are integrated with aging control systems. One example of this intersection of old and new is the relatively recent introduction of WiFi on planes, which some researchers believe makes it much easier for attackers to hack airplanes. While WiFi on planes has a positive impact for the customer, according to the GAO, the introduction means planes may be more susceptible to having their inflight computer systems hacked through on-board networks, or remotely by individuals elsewhere. In fact, the report calls out that “[m]odern aircraft are increasingly connected to the Internet. This interconnectedness can potentially provide unauthorized remote access to aircraft avionics systems.” The aviation industry involves more than just aircraft, of course. In addition to inflight safety, aviation as a whole now has to worry about how to collectively manage a growing number of security issues which target adjacent parts of the business. Threats to air traffic control and reservation systems (GDS/CRS) are numerous. With the air traffic control systems, the primary concern is still flight safety, not financial fraud. The same GAO report above calls into question the FAA’s strategy for cyber security around NextGen, the satellite-based replacement for today’s radar-based air traffic control system. This is another example of newer technology being moved into a field that previously a limited number of people were familiar with. Radar expertise and access to equipment is relatively small, but millions of people use GPS on a daily basis. There are many more GPS experts in the world and this fundamentally changes the threat landscape for air traffic control. With reservation systems, like Sabre, Amadeus, and others, financial fraud is the biggest security issue. One of the key differences between air traffic control systems and GDS/CRS is the eventual connection to the consumer. Anything that involves purchasing and managing transactions, already has multiple users, and eventually interacts with the consumer should be considered a high value target for cyber criminals. These systems are likely to have broad network connectivity, so the threat model involved is substantially different than the threat model associated with air traffic control. The utilization of technology in these systems is different as well; because there are more potential connection points for GDS/CRS systems and they tend to use more off-the-shelf IT. This actually makes GDS systems both harder and easier to secure; harder because these systems present a bigger attack surface and easier because much of the corporate IT security technology exists for many of those components. On the air traffic control side, or any of the more isolated, industrial control-type systems, the impact of an individual security incident is much greater and the adversaries are different. Someone interested in causing a significant air traffic incident has different motivations than someone who is trying to steal money. These two different types of attackers will take different risks and typically have different resources.
Where Does This Leave Disclosure?
Because of the numerous cyber threats to the aviation industry, it is vital that the industry comes together to build adequate security defences. This effort will help detect and protect critical aviation infrastructure from potential cyber-attacks. Effective aviation cyber security requires organizations to build accurate threat models, which will help define and describe the attacks that could compromise safety, or put customer data and financial information at risk. Accurate threat models are the first step toward building sufficient defence capabilities, and the process of creating these models starts by contemplating how systems can be breached and clearly identifying areas of the network most vulnerable to attack. Information security researchers can play a key role in identifying these critical vulnerabilities, but only if the industry resists the urge to suppress research around potential cyber-attacks. Instead, aviation industry organizations should seek responsible partnerships with security researchers. This isn’t a perfect solution, and doesn’t eliminate criminal elements, but most security researchers believe the best approach is responsible disclosure because it minimizes the risk associated with publication and maximizes the effectiveness of vendor response. This model has produced measurable reduction in security risks in other industries, and the potential to improve aviation security relatively quickly is significant. Whether through responsible partnership, or underground research, these vulnerabilities will be discovered. How industry proceeds from here will ultimately affect just how friendly the skies we fly remain.

