
Sextortion scammers are now using potential targets' redacted phone numbers in an attempt to trick them into submitting payment. Perhaps after having obtained a list that ties people's phone numbers and email addresses together, scammers are sending out sextortion emails that use redacted phone numbers to lure in victims. Here's an example, as disclosed by Naked Security:
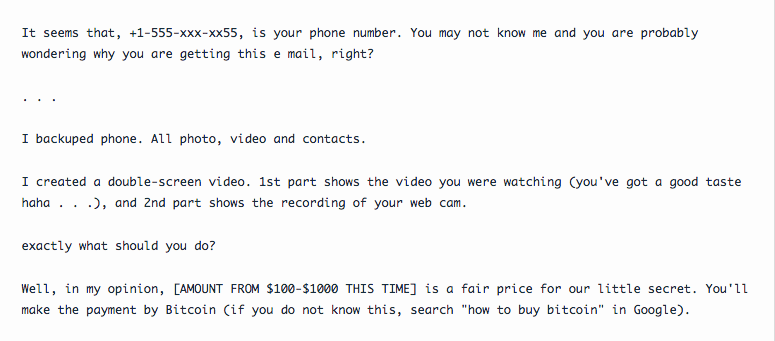
It seems that, +1-555-xxx-xx55, is your phone number. You may not know me and you are probably wondering why you are getting this e mail, right? . . . I backuped phone. All photo, video and contacts. I created a double-screen video. 1st part shows the video you were watching (you've got a good taste haha . . .), and 2nd part shows the recording of your web cam. exactly what should you do? Well, in my opinion, [AMOUNT FROM $100-$1000 THIS TIME] is a fair price for our little secret. You'll make the payment by Bitcoin (if you do not know this, search "how to buy bitcoin" in Google).
Of the 5,000 instances of this scam received by Naked Security, many had the same five digits redacted, though there were a few with all but the last four digits censored. Each of the scam messages directed victims to transfer Bitcoin to one of three addresses. At the time of publication, those addresses showed 20 payments ranging in value from $1 to $1000. It's unclear whether those payments were directly related to the scam. The emergence of this ploy hasn't stopped sextortion fraudsters from using breached passwords to demand payment from users, either. Wendy Nather, Director of Advisory CISOs at Duo Security, confirmed as much on Twitter. https://twitter.com/wendynather/status/1029844406436646912 Whether scammers are leveraging redacted phone numbers of breached passwords, users are urged to not meet the fraudsters' demands. The scammers don't have any incriminating or embarrassing on their targets. And even if did they have a user's sensitive materials, Naked Security rightly noted that paying now won't stop them from sending additional sextortion messages in the future. Users should instead spend their time defending themselves against similar scams by protecting their web accounts with unique passwords and multi-factor authentication (MFA).
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

