
A new sextortionist scam is using spoofing techniques to trick users into thinking that digital attackers have compromised their email accounts. As reported by Bleeping Computer, an attack email belonging to this ploy attempts to lure in a user with the subject line "[email address] + 48 hours to pay," where [email address] is their actual email address. The message informs them that they were infected with a virus sometime between 30 July 2018 and 9 October 2018 after they supposedly visited a malicious website. Through this fake infection, the bad actors claim to have gained access to the user's "messages, social media accounts, and messengers." They also state that they were able to access the user's webcam and record the user while they were watching adult content online. The attackers ultimately demand that the user pays $800 in bitcoin or has their messages and recorded videos sent to their email account's contacts. As of 11 October, users had deposited 0.49179786 bitcoins (approximately $3,054) into the bitcoin wallet operated by the attackers. Below is an example of the attack email sent out by this sextortionist scam variant.
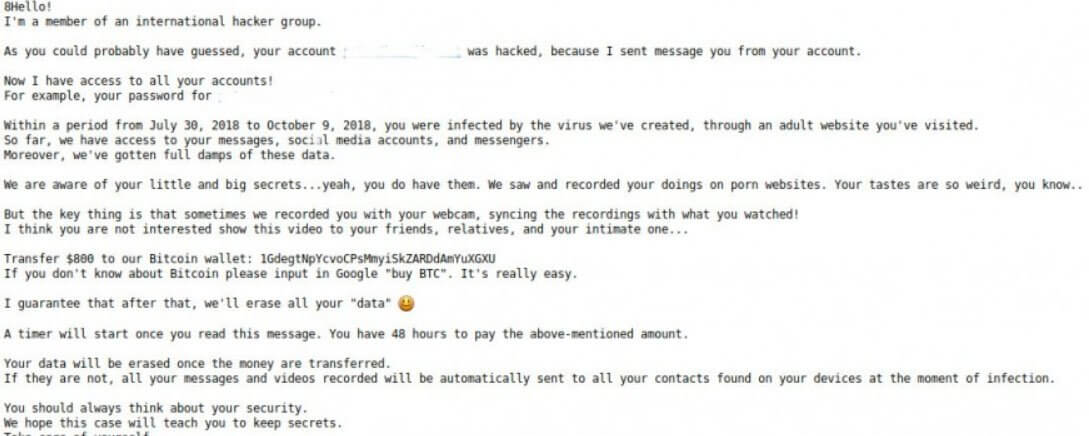
An attack email sent out by this scam variant. (Source: Bleeping Computer) As in other recent sextortionist scam variants, the individuals behind these attack emails are just bluffing. They don't have access to users' email accounts. They're sending spoofed messages that appear to come from someone else. The first instance of this scam variant surfaced in the Netherlands, where attackers made off with €40,000. Not long afterward, a security researcher known as "SecGuru" discovered an English variant of the ruse. SecGuru told Bleeping Computer that email providers can help protect users with Sender Policy Framework (SPF) and Domain-based Message Authentication, Reporting and Conformance (DMARC) frameworks that lock down their domains and prevent bad actors from abusing them. At the same time, users should be on the lookout for an extortion attack that uses urgency and threats to trick people into sending over money.

