
Security researchers discovered that an APT group known as "Silent Librarian" is actively targeting universities with spear phishing attacks. Malwarebytes learned in mid-September that Silent Librarian, also known as "TA407" and "COBALT DICKENS," had launched a new attack campaign. In its analysis of the operation, the security firm found that the threat actor had registered convincing domains to mimic legitimate university websites around the world. These domains predominantly relied on the .ME top-level domain followed by .TK and .CF. Silent Librarian also used Cloudflare for most of its phishing hostnames, as uncovered by Malwarebytes, although the group did tie at least some of its infrastructure to hosts located in its home country of Iran.
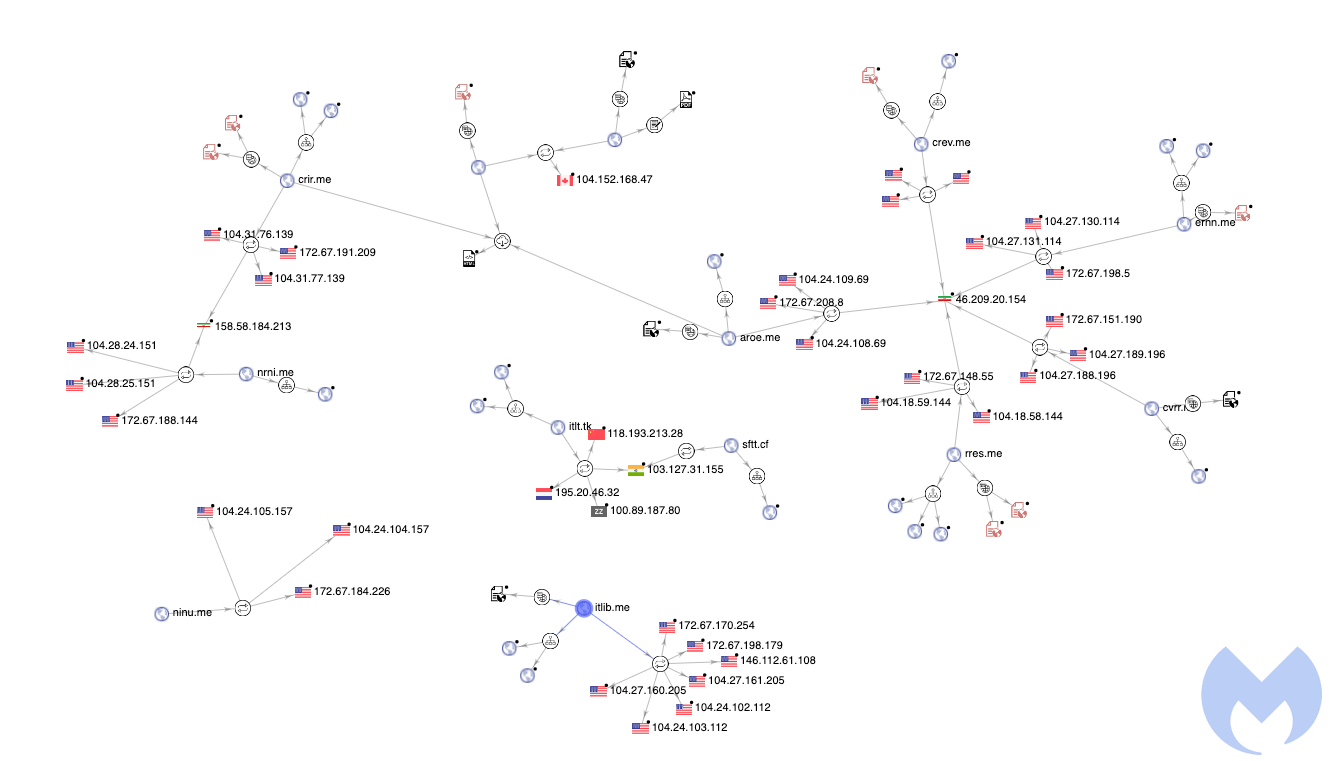
Part of the phishing infrastructure showing connections with Iran. (Source: Malwarebytes) This isn't the first time that Silent Librarian has targeted universities. In 2018 and 2019, Secureworks and Proofpoint uncovered attack campaigns in which the APT group targeted universities in over a dozen countries. News of those attacks arrived shortly after the Department of Justice indicted nine Iranians for attempting to steal information from universities and other organizations. The ongoing resilience of Silent Librarian highlights the threats confronting organizations in the education sector and the need for these entities to protect themselves against phishing attacks. PJ Norris, senior systems engineer at Tripwire, elaborates:
Universities are fruitful targets for cyber attackers and malicious actors. Intellectual property theft motivates many of the targeted attacks such as spear phishing academic staff. However, universities have large collections of personally identifiable information for their faculty, staff and students, and this provides significant motivation for attackers. Employee education is the first line of defense against phishing, but even trained security professionals can be fooled by a well-crafted attack. Organizations should put in place technical controls to prevent and detect successful attacks, as well. It’s not enough to simply tell people not to click on dangerous links.
Tripwire's solutions use file integrity monitoring and secure configuration management to help organizations manage and address network changes that could be the result of a phish. For more information on how Tripwire's products can keep your organization safe, click here.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

