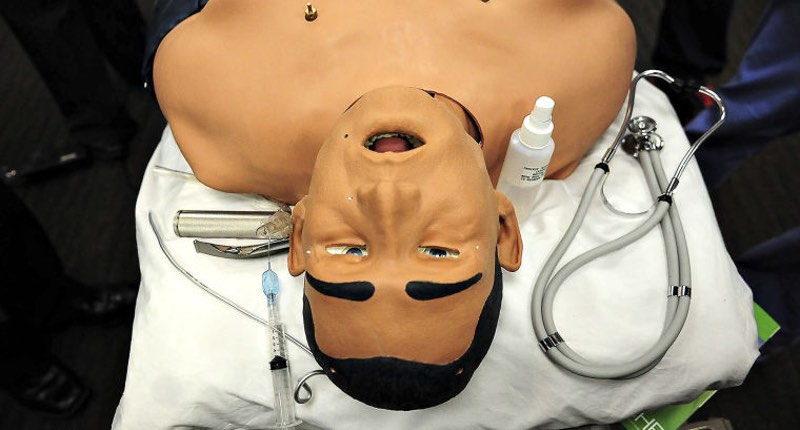
Yes, simulated humans exist. And even if they don't quite walk amongst us, they do lie in beds in hospitals, helping medical students get valuable experience in caring for patients without the worry that one wrong step might result in a real human life being lost. Don't know what I'm talking about? Then meet iStan, the "most advanced wireless patient simulator on the market" according to its manufacturer CAE Healthcare:
"iStan is the most advanced wireless patient simulator on the market, with internal robotics that mimic human cardiovascular, respiratory and neurological systems. When iStan bleeds, his blood pressure, heart rate and other clinical signs change automatically, and he responds to treatment with minimal input from an instructor. With wireless operation, iStan can be placed in any field location, including an automobile, and display all the vital signs and signals of a critically ill or injured patient."
If you're unfamiliar with iStan, the $100,000 simulated man, check out this YouTube video from the Pittsburgh Technical Institute introducing their high-tech aid to medical training. It all sounds very cool. But, of course, this is some reasonably advanced technology we're talking about - all controlled from software running on a laptop.
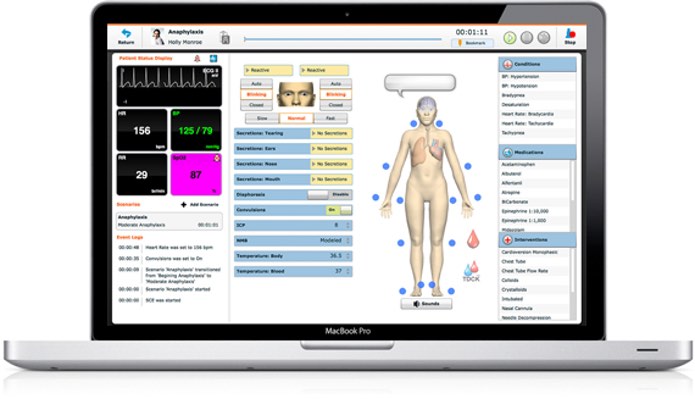
You can probably guess where this story is going... As Motherboard reports, Mike Jacobs, director of the simulations program at University of South Alabama, decided to investigate whether the medical training mannequin was vulnerable to similar types of attacks as those that we see against regular technology. Jacobs and his team investigated attacks which could be launches against iStan, focusing on the communications between it and its controlling laptop's front-end platform that utilises Adobe Flash Player and Muse. In their write-up the team discovered that iStan's operation was vulnerable to denial-of-service attacks, security control attacks, and its PIN security lock could be busted open through brute force:
"The components of the medical mannequin identified as vulnerable to attack in this research include the network security solution and the network protocol. The security solution was breached using an open source brute force attack against the router Personal Identification Number (PIN). The network protocol was attacked through a denial of service attack."
The researchers went on to explain that "for security reasons" they were not publishing the actual PINs or full device MAC addresses. Headlines like that used by Motherboard - "Hackers Killed a Simulated Human By Turning Off Its Pacemaker" - might understandably raise concerns amongst the public and the skyward-rolling of eyes amongst the technical community, but it is true to say that as we connect more devices to each other and to the internet, we must think about the security implications. No-one should panic, but manufacturers and software developers need to ensure that they are doing everything they can to build secure systems that cannot be easily exploited. It may not matter that much if your internet-enabled thermostat goes on the blink for a short period of time, but if cars are vulnerable to remote hacking or medical devices implanted inside our bodies have critical flaws that can be exploited, then much greater care needs to be taken by manufacturers. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.

