
A new spam campaign is attempting to infect German-speaking users with samples of the destructive Ordinypt malware family. According to Bleeping Computer, the campaign sent spam emails masquerading as a job application from someone named Eva Richter. These messages supported this claim by using the subject line "Bewerbung via Arbeitsagentur - Eva Richterwhich," which translates to "Application via employment agency - Eva Richter." They also arrived with a stock photo of the job applicant as well as an alleged copy of her resume and CV called "Eva Richter Bewerbung und Lebenslauf.zip."
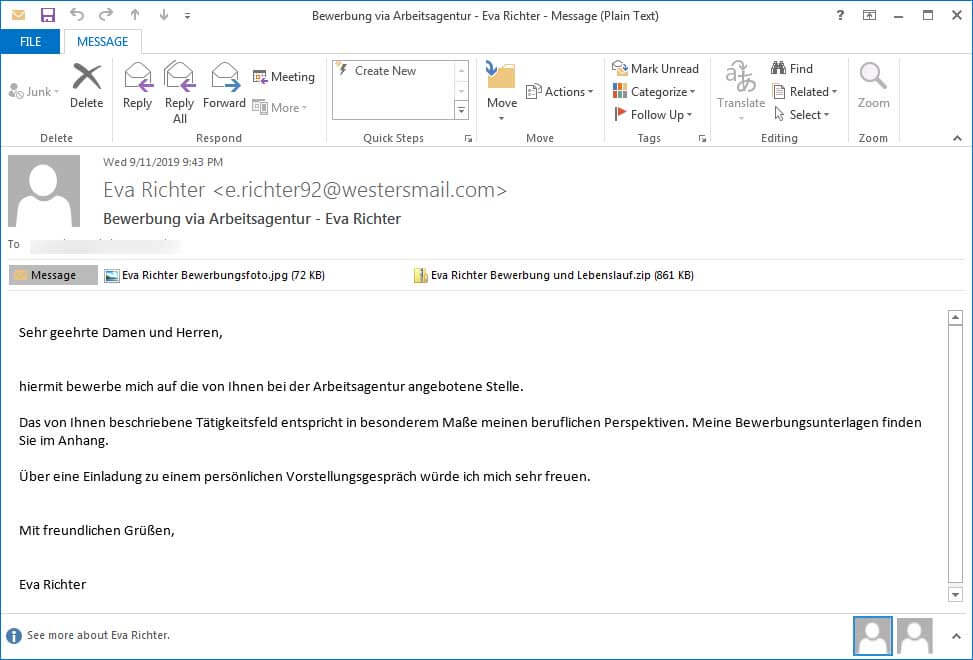
A copy of the spam message. (Source: Bleeping Computer)
[Translated into English] Dear Sirs and Madames, I hereby apply for the position offered by you at the Employment Agency. The field of activity you describe corresponds especially to my career prospects. My application documents are attached. I would be very happy about an invitation to a personal job interview. Yours sincerely, Eva Richter
Once opened, the .zip archive reveals a file called "Eva Richter Bewerbung und Lebenslauf.pdf.exe" that pretends to be a PDF document. Running this executable activates Ordinypt, malware which flashes various colors on the computer screen as it begins terminating processes and appending "encrypted" to files it infects. The threat also deletes shadow volume copies. While all of these behaviors are reminiscent of ransomware, the malware actually doesn't encrypt files but instead overwrites them with garbage. Ordinypt therefore functions as a wiper in that it offers no way for victims to recover their files. This campaign highlights the importance of organizations taking steps to protect themselves against attacks by destructive malware like Ordinypt. Among those steps, organizations should use backups and other techniques to maintain the integrity of their data. They should also consider investing in a sophisticated solution that's capable of protecting their assets against known malware signatures and behavior indicative of zero-day threats. Learn how Tripwire Malware Detection can help.

