
A new Spotify-themed phishing campaign informed recipients that the music streaming service had frozen their subscriptions. On 5 December, MailGuard discovered an email that appeared to come from Spotify. The email itself used the display name "Spotify" along with the music streaming service's logo to lull recipients into a false sense of security. With a subject line reading "Your payment didn't go through," the phishing email informed users that Spotify had failed to successfully process their payment. It went on to claim that the service had paused these users' Premium subscriptions and that those members would therefore lose the benefits of their Premium membership, including the ability to listen to songs offline and without the interruption of ads. MailGuard explains what happened when a user fell for the phishing email's trap and clicked on its embedded "Get Premium" button:
Unsuspecting recipients who click on the link to ‘Get Premium’ are led to a fake Spotify-branded phishing page that asks for their login details. Upon ‘logging in’, users are then taken to a similar-looking page asking them for to update their payment information. These include their credit card & CCV numbers.
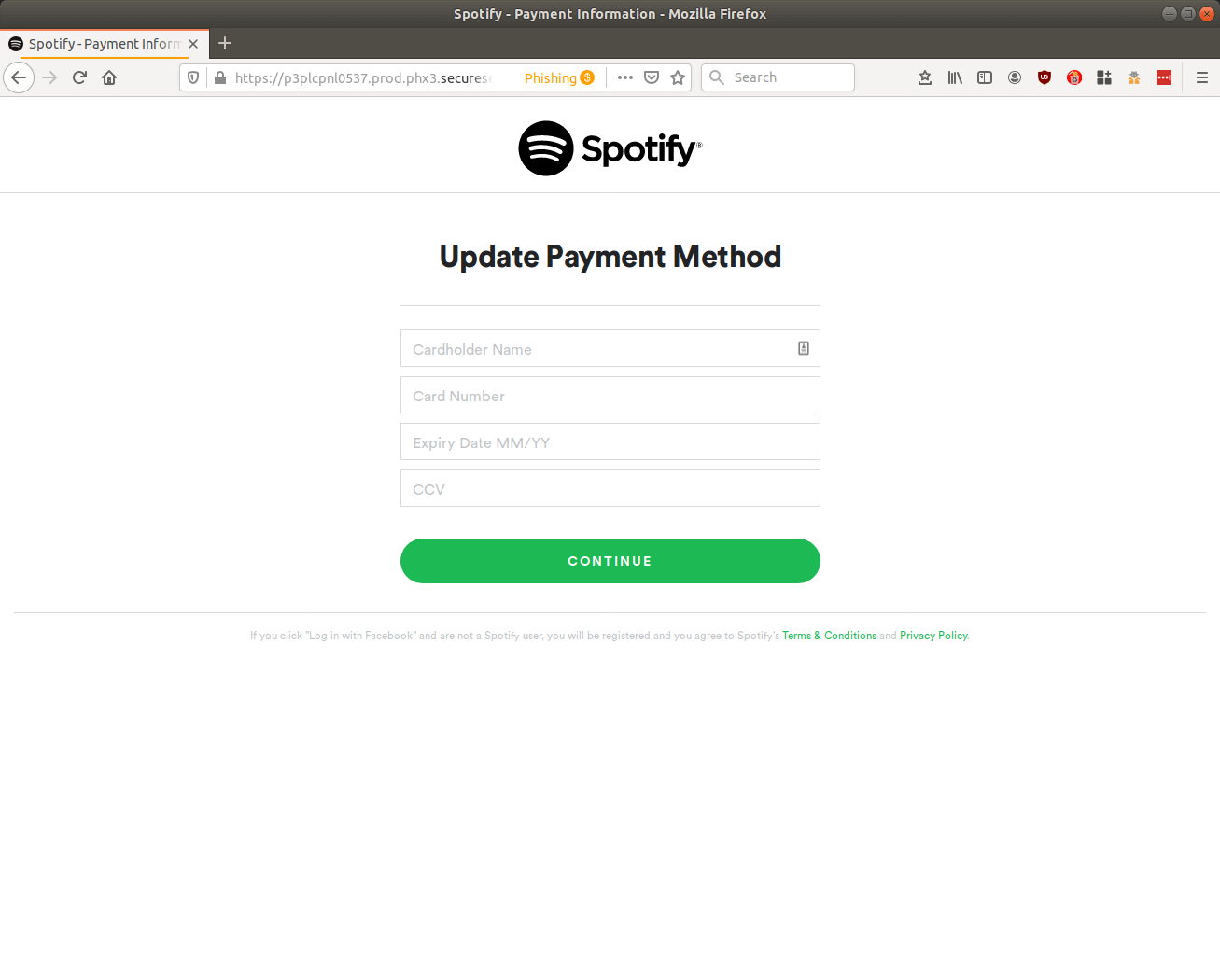
A screenshot of a page from the Spotify phishing campaign that's designed to steal users' payment card details. (Source: MailGuard) Users who entered in their payment card information found themselves redirected to another phishing page that asked them to update their billing details. This page gave malicious actors additional personal data that they could use to further prey upon users via secondary attacks. The campaign terminated by displaying a "404" error page to those users who clicked the "Finish" button. The infection campaign described above illustrates how malicious actors continue to abuse the reputations of respected companies like Spotify to prey upon unsuspected users. Given this ongoing trend, organizations should heighten their email security defenses by educating their users about some of the most common types of phishing attacks that are in circulation today. This resource is a good place to start.

