You would be hard-pressed these days to remain ignorant of the growth of ransomware incidents experienced by organizations large and small. We’ve seen a ton of press around these events, from CryptoLocker to WannaCry. The impact of this type of malware is newsworthy. The landscape of malware is changing, however. While ransomware is still a significant force, there’s (re)growth in other types of malware. In order to get a picture of how things are changing, I pulled the data from the Multi-State ISAC’s monthly Top 10 Malware for 2018 and created this trend chart.
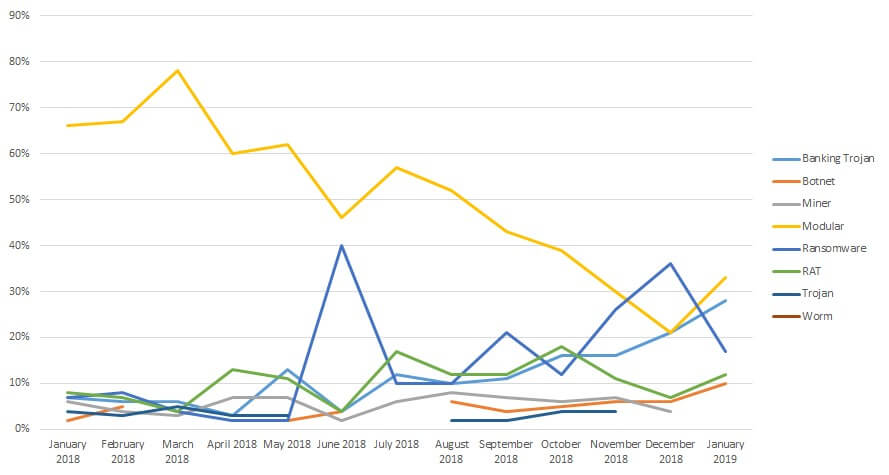
The ‘type’ labels here are mine. The chart shows a decline in reports that involve a modular or loader type of malware, generally used to deliver some other payload. It also shows a slowing growth in ransomware, but the big spikes are notable. The other category to pay attention to, because of its steady growth, are the banking Trojans. The key conclusion here, I think, is that ransomware is only one type of malware that you need to worry about. It’s not even or always the most prevalent. This conclusion is supported by other data sources. Ransomware is on the decline. Ransomware is different, however. Its characteristics differ from other malware in meaningful ways. First, ransomware has to announce itself in order to get the ransom paid. It’s designed to be discovered. Second, it requires user action to pay the ransom, and it requires the attacker to take action (providing a decryption key) when the ransom is paid. Finally, once it’s been successfully executed, the target is effectively burned. Ransom is generally paid only once. Compare those characteristics to other malware that needs to be stealthy, to avoid user interaction and to persist as long as possible. These differences mean that defense has to be different, as well. If your focus on malware defense is solely on ransomware, then you’re missing significant parts of the puzzle. Malware defense can be thought of as existing in three phases: prevention, detection and remediation. Each of these phases benefits from a set of security controls, and we’ll explore each of them below.
1. Prevention
The lowest-cost way to deal with malware is to avoid an incident completely, and that’s the objective of prevention. We should also be concerned about preventing malware from spreading. Almost any security control could be relevant for preventing malware, but there are a few that stand out. Malware doesn’t magically appear on your systems. It has to get there through some means, and prevention is largely about limiting those means. Secure Configuration Management Building a solid foundation is the best place to start for an effective defense. That means putting in place and managing secure configurations for the assets in your environment. In order for this control to be effective, you must be able to define what a secure configuration is for those assets, and you have to be able to validate that an asset is configured to meet that standard. If you don’t start with secure configurations, then you are simply leaving the door open for malware. Vulnerability Management You can think of Vulnerability Management as a part of secure configuration management. After all, a secure configuration is one that meets your requirements for vulnerability risk. Malware often exploits a vulnerability of some kind in order to get installed on a system and, as such, finding and remediating vulnerabilities is a key defense. Integrity Management If you can effectively start with a secure environment, then you have to worry about changes that impact the integrity of that environment. Integrity management is the practice of managing those changes against the target of maintaining your environment. It requires that you detect changes and that you assess them for how they impact security. Changes might occur on specific systems, or they might occur in the external threat landscape. Managing integrity can help keep malware out and keep it from spreading if it does get inside. Privileged Identity Management Controlling the use of administrative privileges is a key control because the misuse or misconfiguration of privileged accounts is a common mechanism for attackers to gain entry or spread in an environment. Workstations or laptops running as admin are ripe for abuse and much easier to install malware on. Email Security Phishing and other email-based attacks are a common entry point for malware of all kinds. While you may not be able to prevent 100% of malware coming in, if you’re not implementing this most basic control, you’ll be the victim of opportunity more often than not.
2. Detection
Detection is what jumps to mind for most people when we talk about malware defense, and it is an important part of the overall picture. The goal here is obviously to identify malware that’s in your environment, ideally before it gains a foothold. Anti-Malware Tools Most people think of standard and advanced anti-malware tools when they think of detection. And that’s not wrong. Putting in place basic, foundational security controls is important. If an off-the-shelf anti-malware tool can detect malicious software on the network or on a host, that’s great. Don’t let the brevity of this paragraph fool you; there’s a whole industry behind anti-malware tools, and it’s competitive. It’s important to realize, however, that while these tools are always improving, none of them are perfect yet. That’s why there are other controls to consider for detection. Change Detection Every incident starts with a change, and that’s true for malware infections as well. With very few exceptions, malware has to make some kind of a change in the environment. Malware that slips past standard defenses can often be identified by the changes it leaves in its wake. New files on a system, changes in settings, changes to logging and a variety of other suspicious changes are all worth investigation. A good change detection system can not only surface those changes but can filter out those that are business-as-usual so you can focus on the suspicious changes. Log Management Another stalwart of detection is log management. Collecting and analyzing logs isn’t new, but it continues to be a key control for identifying both initial malicious activity related to malware and for tracing the extent of an infection. If you haven’t implemented comprehensive log management, you’re flying blind. Suspicious File Detonation If you do find a suspicious file in your environment that wasn’t caught by your malware detection tools, you need the ability to analyze it. This is where malware sandboxing tools come in. These are tools that execute (or detonate) a file and analyze its behavior. The analysis tells you if the file is malicious, suspicious or benign. This is an advanced malware detection capability, but it’s invaluable if you’re already tooled to identify suspicious files in your environment.
3. Remediation
If you do detect malware in your environment, you obviously need to take steps to address it, and that means remediation. It might seem like the objective here is as simple as ‘remove malware,’ but there’s a more expansive objective that’s important to consider. The goal is to return your environment to a trusted state. If you remove the malware but fail to restore trust, you’ll just end up with another incident. With that in mind, the security controls here are also more expansive. Anti-Malware Tools The first place to start with malware removal is with the standard anti-malware tools. This is where you would quarantine or remove malware first. Removal of known malware is the first step in getting back to a set of trusted systems, but it’s certainly not the last. Backups You might think of backups as necessary in case of data loss, and that’s true, but restoring from a known-good backup is also necessary to restore trust. An environment that’s been compromised is no longer trustworthy, so being able to turn back the clock to a known-good state is a good way to restore that trust. Configuration Management For cases where you can’t nuke and pave from backup, you’ll need to rebuild to a trusted state, and for that, you’ll need a way to understand what a trusted state looks like. Establishing and maintaining known-good baseline configurations is a way to do just that. If you can baseline your systems’ configurations and then maintain that baseline through changes that occur, then you can always know what a ‘trusted state’ configuration looks like. That can be your guideline for rebuilding and configuration systems after an incident.
In Summary
Throughout the three phases of prevention, detection and remediation there are opportunities to improve your malware defenses. If you focus on only one type of malware, you’ll leave yourself at risk for others. These security controls are best practice in general but also specifically address the infection vectors for malware.
For further insight, watch the Infosecurity Magazine webinar with Tim Erlin called, "The Death of Ransomware: Long Live Other Malware."
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

