
Yes, targeted attacks - especially those perpetrated by an adversary with considerable resources, such as a foreign state - may incorporate zero-day vulnerabilities, but often they begin with something as simple as a phishing message tricking your staff into handing over their passwords. That's a lesson you learn from a new report published by Microsoft that explores a pernicious hacking gang that has concentrated its efforts into breaking into computer systems belonging to government bodies, diplomatic, and military institutions in NATO countries and into some parts of Eastern Europe. The gang (called Strontium by Microsoft, but also known as APT28, Sednit, Sofacy and Fancy Bear by other researchers) is thought to identify potential targets from mailing lists, public forums and social media sites, and then use spear phishing techniques to steal login credentials. For instance, Microsoft describes how the group sent out bogus "Privacy alert" emails, telling recipients that an attempt had been made to access their accounts from Ukraine, and that if it was not them they should change their password by following a link. Because many of the people targeted would have access to sensitive information, there is a strong likelihood that users would be keen to ensure that their accounts were secure and click on what was - in reality - a phishing link.
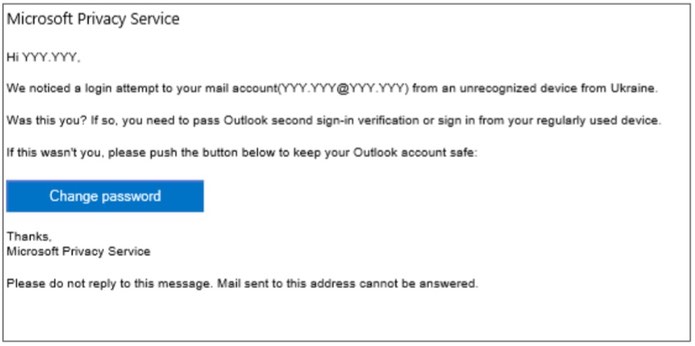
As Microsoft expains, the Strontium hacking gang had a number of spoofed domain names under their control to increase the chances of success for such attacks.
| Legitimate domain name | Spoofed domain name controlled by STRONTIUM |
|---|---|
| accounts.google.com | accounts.g00gle.com |
| us-mg6.mail.yahoo.com | us-mg6mailyahoo.com |
| profile.live.com | privacy-live.com |
| mail.ukr.net | mail-ukr.net |
| www.nato.int | nato-news.com |
| www.bbc.com | bbc-press.org |
| www.ocse.org | osce-press.org |
| www.eff.org | electronicfrontierfoundation.org |
Even if a user isn't tricked into entering their login details, the very act of clicking on a link can reveal details about the target's web browser and the operating system that they are using. The attacker may even be able to determine what browser add-ons and plugins are in use, providing valuable intelligence for any future drive-by download attack. Hacking into a target's accounts is one way for hackers to scoop up valuable data. But they are also interested in infecting a target's computer with malware. Again, the methods used do not have to be remarkably sophisticated - emails can contain malicious links designed to infect PCs or might carry a poisoned attachment. It is the care taken in the email's disguise that will determine its chances of success.
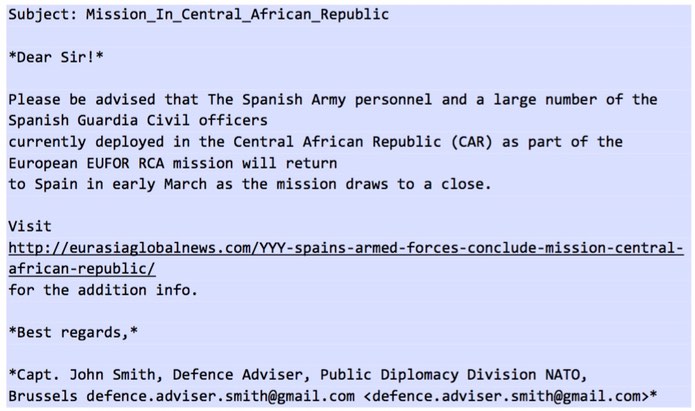
It is at this point that a zero-day vulnerability might be used, exploiting software flaws that have not yet been patched. The Strontium hacking group seems quite comfortable exploiting flaws in a wide range of products, including Adobe Flash Player, Java, Microsoft Word and Internet Explorer. Microsoft reports that the Strontium gang deployed a "number of zero-day exploits" disclosed following the hack of private Italian spyware firm Hacking Team earlier this year. In this way, computers are compromised and information stolen through backdoors that are installed. Intriguingly, the Strontium hacking gang also deploys a component specifically designed to infect connected USB storage devices, helping the criminals to steal information from air-gapped computers that are not on the network when a user transfers a USB device to an air-gapped PC and then back again. Much more information about the threat can be found in Microsoft's report, and it's clear that institutions should take steps to reduce the probability of a successful infection by reducing their attack surface. One of those steps, undoubtedly, should be to raise awareness amongst staff about the methods used by cybercriminals, and to teach them to be on the look out for targeted spear-phishing attacks. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

