
The internet is full of personal and business-sensitive information if you know where to look. In a previous post, we detailed our method of collecting Open Source Intelligence (OSINT) by “scraping” the content posted to public websites where stolen information is regularly released by hackers. That post focused on email and password combinations (over 1.5 million of them in the past year) that have been anonymously posted on these types of sites. The release of these credentials poses a serious potential risk to affected users and organizations. However, credentials are not the only type of potentially sensitive information that is regularly posted to these sites.
IP addresses are used to identify particular resources on the internet, much like a street address might identify a person. Over the past year, over 3.8 million unique IP addresses have been released on sites such as Pastebin.com. For individuals, this does not represent a serious source of risk. But an organization might want to understand why the IP address of their corporate firewall, VPN, or web application has appeared on a website that is routinely accessed by hackers. Upon a closer examination of the vast IP address dataset collected over the past year, it was noted that IP addresses were released for malicious reasons, as well as benign.
For example, OCD Tech has captured “target lists” containing the IP addresses of hosts that are potentially vulnerable. Attempts to exploit and breach the resource hosted at an IP address are also regularly made public, including attacks against web servers and firewalls. Also, lists of IP addresses that have been compromised and are now hosting malware have been identified on the websites monitored by the scraper. While the majority of IP addresses released to Pastebin and similar sites may not represent an active threat, there are other reasons to monitor for your corporate, client and vendor IP addresses.
For instance, IT support personnel may be posting system logs to these public websites, which is a common practice for sharing logs when collaborating on an issue. Further, developers may be posting proprietary scripts or application code, as code-sharing is what these sites were originally designed for. These situations can lead to unauthorized or unintentional release of intellectual property or sensitive information about the systems in use by the organization. If an IP address your organization owns appears anywhere on these sites, you'll want to know.
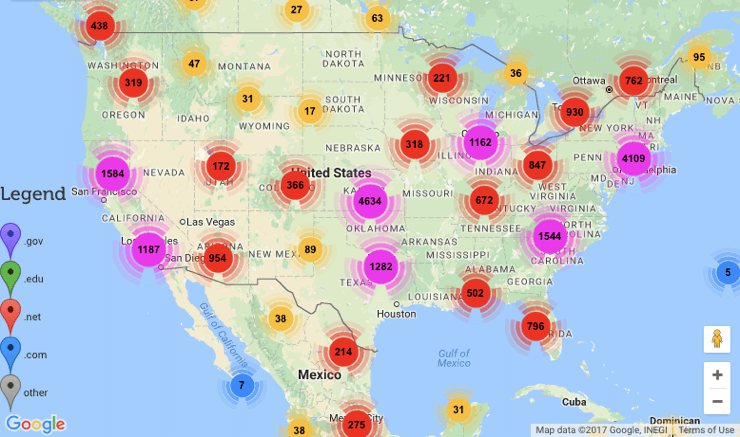
Then, you can evaluate the context to determine the type and level of threat you face and what steps you can take to mitigate it. To help visualize this massive body of data, OCD Tech’s Rachel Berman has developed an interactive map showing the geolocation of a subset of IP addresses that appeared on Pastebin.com and similar sites.
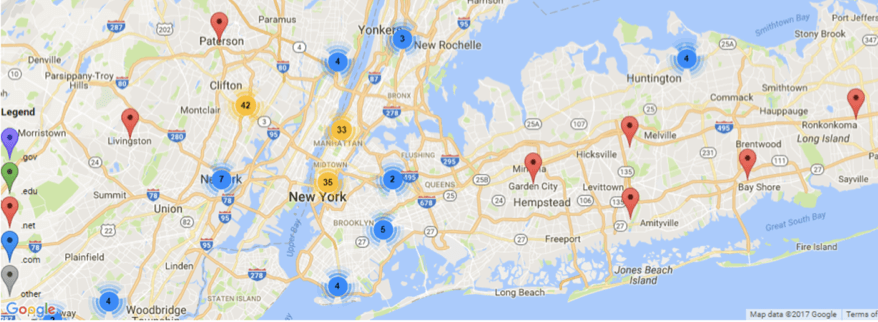
The site shows over 18,000 IP addresses found in the span of one hour, 3-4 PM EST on July 19, 2017. This is an arbitrary time chosen to limit the amount of displayed data to that which can reasonably be displayed on the map. For each of these IPs, it runs a DNS ‘whois’ query to find out to whom the IP is registered and what the associated domain name is.
It then uses MaxMind’s GeoLiteCity database to determine roughly the latitude and longitude. All locations are then added to a custom Google Map. The IP address of any point can be viewed by hovering over the point. All latitudes and longitudes given should not be treated as necessarily accurate. Any IP used by a private individual is typically placed at the headquarters of their internet service provider.
All markers are put in the geographic center of the smallest region given. For example, many IPs are known to be in the US, but no other information is known. They are all placed in the center of the country (specifically, a reservoir in the middle of Kansas).
This results in a lot of points being in the exact same location. To make the individual point viewable, we’ve randomly offset all locations slightly, so that if you zoom in far enough, you can see most if not all of the individual points even if there are hundreds in the exact same location. Your IP isn’t private information; anyone can look it up from your website.
It being posted publicly on sites frequented by hackers doesn’t necessarily mean you were hacked but it certainly doesn’t mean anything good. If you find your IP there, it could be an indicator of an active or emerging threat. IP addresses are part of your organization’s identity on the internet, so check out our map to see if any IPs were released near your organization and remember that this is merely a minuscule fraction of the total data set.
About the Author: Scott Goodwin is an Experienced IT Security Analyst with OCD Tech. He graduated with a Bachelor of Science in Physics from the University of Massachusetts-Boston in May of 2015. His primary engagements are IT vulnerability assessments, NIST 800-53 and 800-171 assessments, and security advisory services. He is also currently working on several research projects related to open source intelligence and penetration testing. You can follow Scott on Twitter, LinkedIn or on OCD Tech's blog.
Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor and do not necessarily reflect those of Tripwire.

