
Security researchers spotted Trickbot malware checking the screen resolution as a means of evading analysis on a virtual machine (VM). Digital security firm MalwareLab came across a sample of the trojan that checked to see whether a computer's screen resolution was either 800x600 or 1024x768. It then terminated if it found that the screen resolution matched either of those specifications.
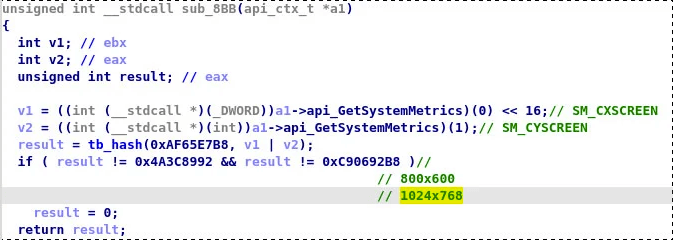
The screen resolution check performed by Trickbot. (Source: Bleeping Computer) These particular screen resolutions aren't arbitrary. Bleeping Computer explains that those settings both have to do with how security researchers configure a virtual machine by not installing guest software that allows for better screen resolutions:
The software is not installed as malware commonly checks for files, registry keys, and processes used by the virtual machine guest software. Without the guest software, though, a virtual machine will typically not allow any resolutions other than 800x600 and 1024x768, compared to ordinary screen resolutions that are much higher.
As a result, this new check helped Trickbot to determine whether it had landed on a virtual machine and in security researchers' cross-hairs. It terminated itself if it discovered the presence of those screen resolutions, thereby preventing security researchers who were using a VM from analyzing it. This discovery wasn't the first time that Trickbot made headlines in 2020. Back in mid-April, for instance, security researchers revealed that Trickbot was the most prolific malware in terms of COVID-19 lures. That was less than two months before analysts uncovered a malicious email campaign that leveraged a fake Black Lives Matter voting campaign to distribute Trickbot malware. The operations described above highlight the need for organizations to defend themselves against a malware infection using a tool that examines suspicious file behavior in a quarantined environment and delivers reports on important system changes. Learn how Tripwire's File Analyzer can help.

