
Security researchers came across an attack email that leveraged a fake Black Lives Matter voting campaign to distribute Trickbot malware. Digital security firm Abuse.ch found that the attack email pretended to originate from a sender known as "Country administration." Building on its subject line "Vote anonymous about Black Lives Matter," the attack email invited recipients to leave anonymous feedback on the Black Lives Matter movement by filling out and returning an attached document called "e-vote_form_3438.doc."
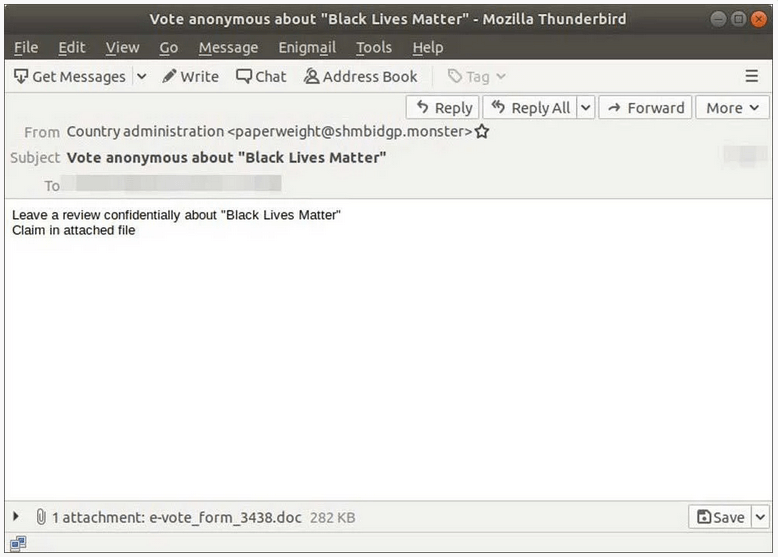
Phishing email (Source: Bleeping Computer) When opened, the attachment informed recipients that they needed to "Enable Editing" or "Enable Content" by clicking on a button. Those individuals who complied triggered the document to run its malicious macros. The code downloaded a malicious DLL onto the recipient's computer and executed it. Bleeping Computer explains what happened next:
This DLL is the TrickBot trojan that, when executed, will download further modules to the infected computer to steal files, passwords, security keys, spread laterally throughout the network, and allow other threat actors to install ransomware. Due to this, a TrickBot trojan can be a devastating infection regardless of whether you are a corporate victim or a home user.
This isn't the first time that Trickbot attracted the attention of the security community in 2020. In mid-April, for instance, Microsoft revealed that the malware had thus far been the most pervasive malware operation to exploit the coronavirus 2019 (COVID-19) pandemic as a theme. In one of those attacks, the threat had leveraged hundreds of macro-laden documents that had pretended to originate from a non-profit offering a free COVID-19 test. The latest Trickbot distribution campaign highlights the need for organizations to defend themselves against phishing attacks. One of the ways they can do this is by educating their employees about some of the most common types of phishing campaigns that are in circulation today. This resource provides an excellent starting point.

