
It seems more and more companies are beginning to understand the benefits of running a bug bounty program, encouraging vulnerability researchers to report security flaws responsibly (for a reward) rather than publishing details on the web or selling a flaw to potentially malicious parties. The latest high profile firm found running a bug bounty is United Airlines. And rather than offering the conventional cash rewards, United is offering airmiles instead. Well, I guess it's better than a corporate t-shirt. Yes, you can win up to one million United award miles if you uncover high severity vulnerabilities, such as remote code execution. But, United's bug bounty program webpage explains, you had best make sure that you are a signed-up MileagePlus member "in good standing" first, in order to qualify for the reward points.
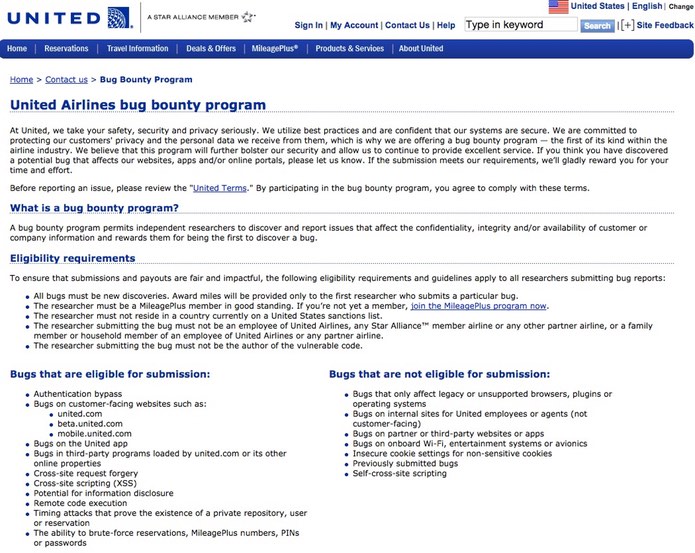
There are some other important rules that are worth bearing in mind too. United says that vulnerabilities which only exist on unsupported browsers or operating systems aren't eligible for the bounty, nor internal customer-facing sites used by employees or agents.

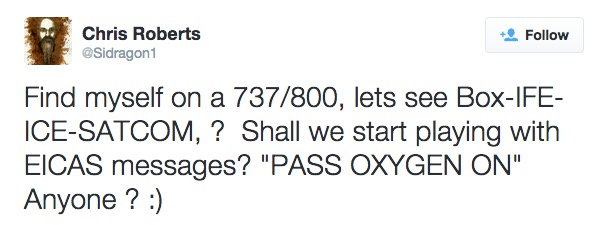
Furthermore, and interestingly in light of recent concerns about the possibility of in-flight hacking of airplanes, they don't want you seeking reward for any bugs you might find in onboard Wi-Fi, entertainment or avionics systems. Hopefully United's position is not that they wouldn't consider such vulnerabilities as being serious, but rather that they are loathe to having researchers attempting to find flaws in a plane that's flying at 30,000 feet. In fact, the airline says that if you conduct any testing on aircraft or aircraft systems then you will be permanently disqualified from the bug bounty, and could face possible criminal action. Ouch! One presumes that United was keen to introduce that part of the small print, following the high profile incident involving security researcher Chris Roberts recently when he was removed from a flight for a joke tweet about possible vulnerabilities.
United will be similarly unimpressed if you attempt a brute-force attack against its servers, attempt to inject code into live systems, or compromise any MileagePlus accounts that don't belong to you. Vulnerability scans of United's servers are also, apparently, a big no-no. My advice is that if you're unsure whether a particular line of vulnerability investigation would incur United's wrath, you should ask them at [email protected] before you proceed. But it's good to see United welcoming vulnerability reports into the security of its customer-facing servers and apps, as it shows they're keen to protect their customers' privacy and prevent hackers from exposing databases or brute-forcing booking details or PINs and passwords. Earlier this year, it was reported that thousands of customer accounts belonging to frequent fliers with American Airlines and United had been compromised, with hackers audaciously booking themselves several free trips or upgrades as a result. A number of other organisations, including British Airways and Hilton, have also recently found their loyalty programs suffering at the hands of hackers. So, all in all, United's bug bounty sounds like a positive step—that other airlines might do well to follow.

